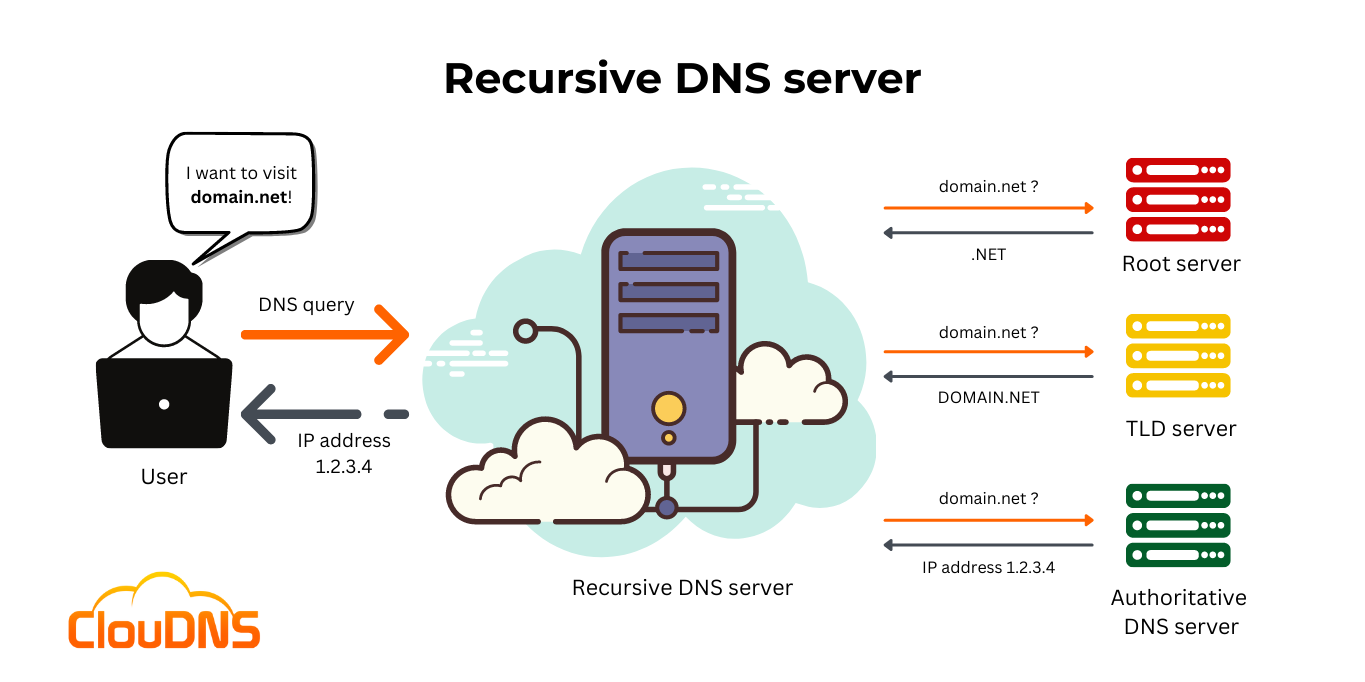
When you browse the internet, you don’t write IP addresses to go to the pages you want; you just write the domain. In the “backstage”, every request that you do, passes through a DNS query. It first goes to your internet provider’s Recursive DNS server. If it can’t find in the cache, the information needed, it will continue to other recursive servers until it gets to an Authoritative DNS server who can give the IP address of the required domain. Basically, it is a name server, that is a middle-man between you, the user, and the Authoritative DNS server.
Table of Contents
Recursive DNS server explained
The Recursive DNS server called, also commonly DNS resolver, has the important responsibility of seeking requested data and responding to users’ DNS queries.
In computing, when we talk about recursion, it is clearly associated with a technique that aims to solve a particular problem. In addition, that involves a program or solution that continuously repeats itself until it reaches the desired goal.
A Recursive DNS server is positioned to function in the middle between the Authoritative DNS server and the end-users that initiate DNS requests. So, each time a user desires to visit and explore a particular website, it types its domain name into the address bar of the browser. From there, the Recursive DNS server receives the request and starts searching for the IP address (IPv4 or IPv6) that corresponds to the domain name. Shortly after the required IP address is found, the DNS resolver returns to the user’s device and provides the needed information. Then the browser on the device (smartphone, laptop, computer, etc.) of the user is able to connect and load the desired website.
The number of available Recursive DNS servers all over the world is significant. However, the most popular among them are the ones of the Internet service providers (ISP).
Tasks of the Recursive DNS server
The role of the DNS resolver is to complete one of the following tasks:
1. Checks if the IP address is stored in the cache memory. There is a certain period of time, pre-defined by the domain’s owner called Time to Live or TTL. It says for how long the Recursive server can hold the information. If it is still there, it will return the answer fast and won’t take further actions.
2. Searches for the IP address elsewhere. If it is not in the cache, it will continue the searching process until it gets to an Authoritative server which has the information.
Ready for ultra-fast DNS service? Click to register and see the difference!Experience Industry-Leading DNS Speed with ClouDNS!
How does it work?
The Recursive DNS server takes a very important role in the DNS resolution process. As we mentioned earlier, it operates between the user and the Authoritative DNS server. Yet, it completes several crucial tasks. Let’s summarize how it operates and what actions it performs in this vital process:
- The DNS resolver is the one that obtains the DNS query from the user.
- It then asks the Root server about the location of the TLD (Top Level Domain) server.
- The Recursive queries the TLD (Top Level Domain) server for information about which is the accountable Authoritative DNS server for the precise domain.
- It makes a request to the Authoritative DNS server responsible for the particular domain.
- The Resolver gets back to the user and provides the requested data.
- It caches the DNS information for further use.
The existence of Recursive DNS servers is crucial. This is because they support the Authoritative DNS servers, which would not otherwise be able to handle the workload created by themselves. Additionally, DNS Resolvers distribute the load of the huge number of user requests and make the resolution of domain names way easier.
Check out Fantastic Premium DNS service plans by ClouDNS!
Recursion and Iteration: Explaining the Dynamic Duo
Recursion and iteration are two programming concepts that play a crucial role in the functionality of DNS servers, particularly recursive ones. Let’s explore these concepts:
- Recursion
Recursion, in the context of DNS, refers to the process where a DNS server, upon receiving a query for a domain name, doesn’t have the necessary information in its cache and initiates a series of requests to other DNS servers to resolve the query. Each subsequent request dives deeper into the DNS hierarchy until the authoritative DNS server for the queried domain is reached.
Imagine recursion as a detective following a trail of clues to solve a mystery. The DNS server starts with limited information, asking other servers for more details until it discovers the complete answer. This recursive process ensures that even if a DNS server doesn’t have the needed information, it can still find and deliver a response after consulting other authoritative sources.
- Iteration
Iteration, on the other hand, involves repeating a set of instructions until a specific condition is met. In the DNS context, iteration occurs when a DNS server sends iterative queries to authoritative servers and, at each step, refines the search until it obtains the precise information needed to resolve a domain name.
Think of iteration as a systematic approach where the DNS server persistently refines its search, step by step, until it comes to the solution. This process allows for efficient querying, minimizing the chances of overwhelming authoritative servers with unnecessary requests.
- Recursion and Iteration in Recursive DNS Servers
Recursive DNS servers blend recursion and iteration to navigate into the complex DNS hierarchy. When a recursive DNS server receives a query, it first checks its cache to see if the information is available. If not, it starts a recursive process, reaching out to authoritative servers and using iteration to specify its search for the required data. This dynamic dance between recursion and iteration ensures that DNS queries are resolved quickly and accurately.
The Benefits of Recursive DNS Servers
Now that we’ve explained the meaning of recursion and iteration let’s explore the benefits that Recursive DNS servers bring to the table.
- Enhanced Performance and Speed: Recursive DNS servers significantly improve the speed of DNS resolution. Maintaining a cache of previously resolved queries allows these servers to respond promptly to reappearing requests without crossing the entire DNS hierarchy again. This results in faster load times for websites and a smoother browsing experience for users.
- Reduced Network Latency: With their ability to store and reuse resolved queries, Recursive DNS servers help minimize network latency. By reducing the time it takes to get information from authoritative servers, these servers contribute to quicker and more responsive internet connections.
- Improved Security: Recursive DNS servers can protect users from malicious activities. Through features like DNS filtering and blocking known malicious domains, these servers safeguard against phishing attacks, malware, and other online threats. They can perform detailed checks and validations before serving DNS responses, adding an extra layer of security to the online experience.
- Load Distribution and Balancing: Recursive DNS servers contribute to the efficient distribution of network traffic by balancing the load on authoritative servers. These servers reduce the load on the DNS infrastructure by caching and serving responses locally.
- User Privacy: They can enhance user privacy by implementing features like DNS over HTTPS (DoH) or DNS over TLS (DoT). These encryption protocols add a layer of security, preventing unauthorized parties from intercepting and monitoring DNS requests.
Vulnerabilities
Cybercriminals are well aware of the importance of Recursive DNS servers. Unfortunately, they managed to use their vulnerabilities and initiate different malicious attacks. Some of the DNS resolvers are public, which makes them an easy target. Attackers often use DNS spoofing attacks or execute DDoS attacks in order to shut the servers down directly.
- Recursive DNS servers and the amplified attacks
DNS Amplified Attacks are a very common threat on the Internet. They exploit the public Recursive DNS servers to generate high traffic and to damage the target.
- Public (Open) recursive DNS
To leave your Recursive DNS server public is dangerous. Such devices are with minimum security and visible IP address. This means that anyone, including cyber-criminal, can easily access it and later use it as a botnet device to amplify their next attack.
Many of the network administrators don’t know their recursive servers are open, and this can lead to severe problems. If you doubt about your DNS server, you can check it on this page: http://openresolverproject.org
- Oversized packets
A threat that some of the attackers take advantage of is manipulating the query packets. They send multiple queries to recursive servers, but with a modified IP addresses, directing all of the generated traffic towards the victims. They use many servers, and if the traffic is high, they can crush the victims’ servers.
Can you have safe Recursive DNS servers?
Yes, it is possible to secure your servers. We recommend you to use our Private DNS servers. They are hidden from the public eye and still have all of the premium features like TTL management, Cloud domains, Secondary DNS, SOA Settings and Hourly statistics
You don’t need to get all of them. You can strategically choose just a few of them where you most need them.
Public vs. Private Recursive DNS Servers: Which One Should You Use?
Choosing between public and private recursive DNS servers depends on your specific needs. Each has specific advantages and limitations that fit different scenarios. Let’s break it down.
Public Recursive DNS Servers are free and available for anyone to use. They are usually offered as a service by big names like, for example, Google (8.8.8.8). They offer high-speed resolution, ease of use, and often come with added features such as malware protection and content filtering. Public servers are great for individuals or small businesses seeking a free and reliable solution. However, some public servers log DNS queries, which can raise privacy concerns.
Private Recursive DNS Servers, on the other hand, are designed for exclusive use by a single organization or user. They’re all about enhanced security, privacy, and customization. Businesses can configure private servers to enforce strict access controls, prioritize internal resources, and reduce exposure to external threats. While highly secure, private servers require technical expertise to set up and maintain.
So, which is better? Public DNS servers are ideal for general use, while private servers suit organizations that handle sensitive data or require advanced configurations. For optimal results, many businesses use a hybrid approach: private DNS for internal queries and public DNS for external redundancy.
Recursive DNS in Enterprise Networks
Recursive DNS servers play a critical role in enterprise environments, where the demands go far beyond simply resolving domain names for browsing. In large organizations, a dedicated recursive DNS infrastructure ensures faster internal lookups, reduces reliance on external providers, and improves overall network performance. Enterprises often configure their recursive resolvers to prioritize queries for internal domains, enabling quick access to company resources like intranet sites, file servers, and email systems.
Security is another key reason businesses use private recursive DNS. Administrators can execute strict access policies, filter out malicious domains, and integrate threat intelligence feeds to block phishing or malware before it reaches employees. Features like logging and monitoring also give IT teams better visibility into traffic patterns, which helps with troubleshooting and compliance.
By deploying private recursive DNS servers, companies gain more control over privacy, reduce exposure to external threats, and optimize resolution speed for both internal and external queries. The combination of performance and security makes recursive DNS servers highly valuable for modern enterprise networks.
Conclusion
The Recursive DNS servers are a fundamental component of the global network Internet and the DNS (Domain Name System). The role they play in the DNS resolution process is significant. DNS resolvers simplify and manage to balance the load of numerous DNS requests daily!