The DNS, as you may know, is a really crucial component that, sadly, we often overlook. Don’t be one of those people, and please pay close attention to this article. There is not a single “good” DNS attack, but many DNS attack types are really dangerous and have the purpose of exploiting various vulnerabilities and create serious problems. Let’s see the 5 most dangerous of them and, most importantly, find a way to protect ourselves. A safe business is good business.
Table of Contents
What is a DNS attack? How can it affect me?
The name says it, an attack that targets the Domain Name System (DNS). It can have a different purpose: trying to destabilize it, bring it down, alter information, or another. The DNS is old, and, as you could guess, by itself, it is not the safest infrastructure in the world. But there are extra measures that can really help.
Imagine these two scenarios so you can understand it easier:
- The cybercriminal redirects the traffic that should go to your site, to one that he or she controls. He or she can have a fake page, mimicking yours and steal valuable data from your clients, pretending to be you. The unaware client, do what he normally does. Register and use the page to buy or put information on it. The troubles for you could be big if they take money from the victims.
- A strong DDoS attack can affect your servers, bringing them down. And keep them like this, under attack, for a long time. In practice, an attack can last even weeks. Losing control can affect your clients. Users won’t be able to access and use your services or buy products during the DNS attack. You can lose money and get negative feedback from clients. You can even permanently lose them.
Experience Industry-Leading DNS Speed with ClouDNS!
Ready for ultra-fast DNS service? Click to register and see the difference!
Anybody could be threatened by DNS attacks, even the big companies. Wikipedia, BBC, Blizzard, and many more have suffered different types of attacks, check here. Nobody is safe, and the news will just keep coming.
Most common DNS Attack Types
Here are 5 of the most popular DNS attacks that you should be aware of. It is important to not neglect such threats and take measures for prevention.
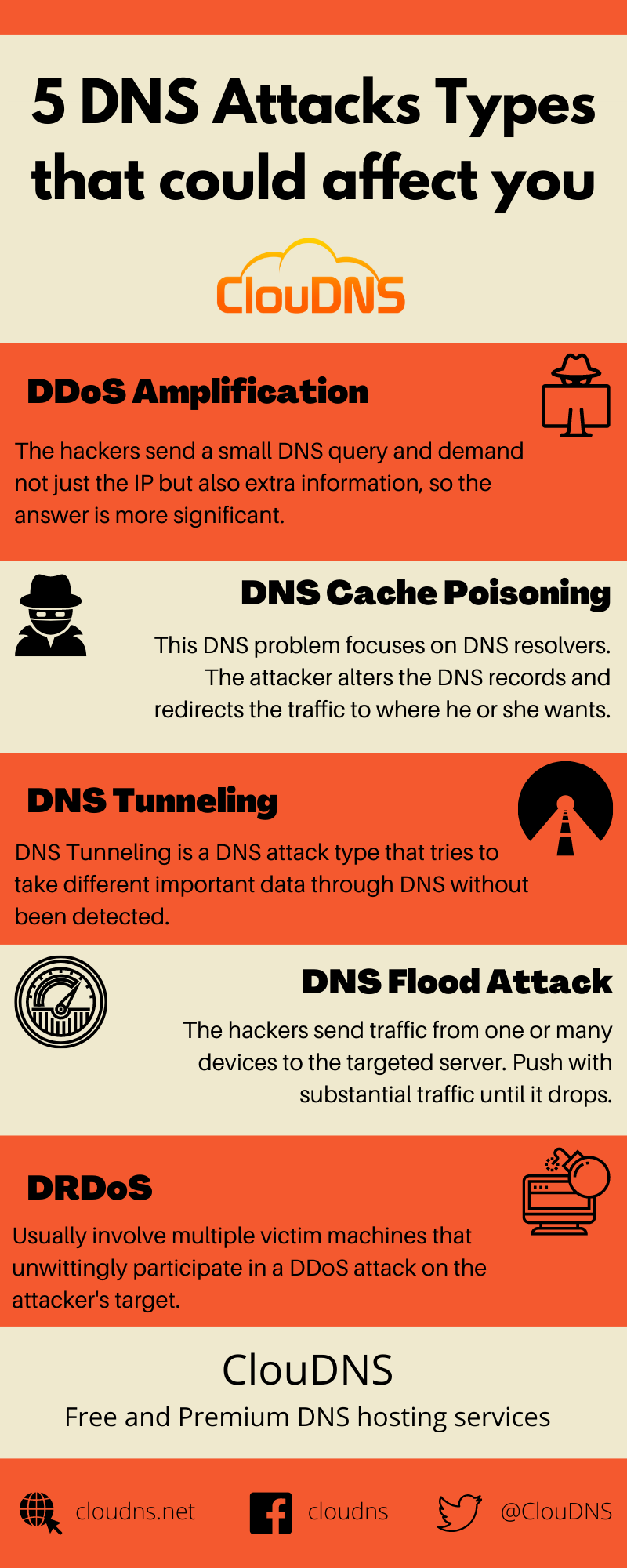
DDoS Amplification
A DNS attack type like this is the one that you will see a lot on the media. With big headlines and big numbers. There are many types, but most often, the amplification attacks exploit the simple UDP protocol. Take it as the weakest link in the puzzle. It doesn’t use verification, and here comes the problem. The goal is to significantly increase, amplify, traffic. The hackers send a small DNS query and demand not just the IP but also extra information, so the answer is more significant. It could be even 10 times larger! The extra trick is that they can modify the request, so the answer goes to the target. That way, the target can get bombarded with many requests that it didn’t want and to experience downtime.
How to mitigate it? You will need a large network of servers (DNS), like an Anycast network. If the capacity is enough, the traffic can be filtered without crippling the network.
Additional measures that you could take are to set a limit to the server, to just listen on only 127.0.0.1 (the localhost). You can, of course, disable the UDP altogether if you don’t use it.
And the third measure is to use a firewall for port 11211 and allowing server access, limited to just whitelisted IPs.
DNS Cache Poisoning
This DNS problem focuses on DNS resolvers. Each of them has a cache memory, where it holds information for domains for a certain amount of time. The Resolvers have a copy of the DNS records and keep them the time that TTL (time to live) indicates. The attacker alters the DNS records and redirects the traffic to where he or she wants (another server). There could be a fake copy of your websites where unaware people will register and give their personal data. This is very common with fake spoofing emails. When the victim clicks on the link, malicious software can then modify the records in the DNS resolver.
You can set limits to the queries to just a specific domain. Also, you can just store the records for a particular domain and no others. Use blacklists to limit.
The best tool to prevent such a thread is DNSSEC. If a Recursive server was poisoned, it wouldn’t continue the query, and then the user will be safe.
DNS Tunneling
DNS Tunneling is a DNS attack type that tries to take different important data through DNS without been detected. A tunnel that you don’t see, but criminals use. It is masked as a DNS query but takes hidden data. A sensitive data can go out unnoticed, and that could cost you dearly.
Your DNS service must have a DNS Protection that acts as an intelligent firewall. But in case you don’t have, you can set up your firewall following the steps:
You will need to have a firewall and add an access rule to block all the unwanted traffic right away. The second step is to make a protocol object in your firewall. You will need to find “Select Protocols”, choose DNS, and there should be “DNS tunnel”. Press it and save.
Create, in the end, an application rule. Again from the settings of the firewall, You will need to specify the trusted connection and then the protocol – “DNS-Tunneling”.
DNS Flood Attack
DNS Flood is a simple and very effective attack. The idea is to send traffic from one or many devices to the targeted server. Push with substantial traffic until it drops. In a way, to flood it with information and submerge it until it drowns. If it is a single source, it is easier to manage, but it can be a huge network of bots that could be tricky to handle.
Flood Attack: Prevention and Protection
The protection exists! It is simple, again DDoS Protected servers. It will have a filtering of dangerous traffic. Also, have an Anycast network with a significant amount of servers that will provide excellent load balancing. Currently, we have 49, that will be a good number. And traffic monitor for showing on time any threads and reacting to the traffic will help.
Distributed Reflection Denial of Service (DRDoS)
A slightly different type from the DDoS attack we just saw. In this case, not the direct queries, but the answers to them will go to the victim. This is the reflection.
The cybercriminals will send DNS queries, but the IP of the source will be changed. Servers will respond and will send all that traffic to the target (The modified IP). The traffic can be overwhelming and flood the target, eventually stopping it. A Smurf attack is a popular DNS attack of that type. Sounds cute, but it isn’t.
The solution again is the same as the one for the DNS Flood type of attack. Get DNS Protected servers. With a proper DNS plan, you will save yourself a lot of troubles. They will have monitoring of the traffic, filters for removing the unwanted requests, a load balancer for heavy traffic, and even more extras for smooth DNS experience.
How to prevent DNS attacks?
Here are some tips that are going to help you prevent, detect, and mitigate a DNS attack.
- Up-to-date DNS software: It is important to use the latest DNS software that contains the latest patches installed.
- Multi-factor authentication (MFA): It is crucial to implement MFA for all available accounts which have access to the DNS infrastructure of your organization.
- Domain Name System Security Extensions (DNSSEC): It ensures the safety of your DNS by utilizing digital signatures based on public key cryptography. That way, DNSSEC adds a very useful extra layer of security to your organization’s DNS.
- Reliable DNS infrastructure: It is the foundation of a safe and protected environment for your organization’s online presence. Anycast DNS network is a must if you receive a lot of DNS requests. However, it will balance the load of an incoming threat.
- DDoS protected DNS: This service is specifically designed to mitigate one of the most harmful cyber threats – DDoS attacks.
- Constant Monitoring: Logging and monitoring outbound and inbound DNS queries and response data can help significantly in detecting abnormal behaviors.
- Keep a private DNS resolver: Restricting the DNS resolver to only users on your network can minimize the risk of malicious external usage. That way, you prevent its DNS cache from being poisoned by cybercriminals.
Motivation behind DNS attacks
One of the most common reasons behind the DNS attack is unfair competitor behavior. Attacking the competition illegally so that it can suffer downtime and all the consequences of it. But there are more:
- Extortion. Do you know how ransomware is getting popular? There is also DNS attack ransomware, where the cybercriminals are using DDoS attacks to target a server. The server can’t respond to regular connections already, and the attackers demand a ransom to stop the attack. The cryptocurrency has facilitated the ransomware process a lot.
- Revenge. The reason behind the attack could be an act of personal revenge against a company, a supplier, or an individual. For example, it is not uncommon that an ex-employee tries to disturb the services of the previous employer.
- DDoS-for-hire. On the Dark Web, the side of the web that you can’t see in Google, there are all kinds of illegal services that you can hire. People hire DDoS DNS attacks to target their competitors. Bringing down their services during important periods. The attack can lead to serious losses in sales for the victim.
- Cover attack. You can imagine the DNS attack as a smoke grenade. Its purpose could be just a distraction. It is taking the attention towards fixing the DNS traffic while another attack is being conducted or malicious software is installed behind the scene.
- Notoriety. Some people want to be famous, even with their bad deeds. Getting some attention for a successful attack could be enough for some hackers.
- Personal challenge. There are smart people who just want to test their knowledge. Such a person might perform an attack, with the only idea to see if he or she can do it.
- Cyberwarfare. Some countries use DNS attacks to target other countries, military groups, separatists, opposition, and even media sites sometimes. The goal is to silence or disrupt the communication of the targeted organization entirely.
- Gamers’ wars. Gamers are very connected with technology. They use DNS attacks to damage the score of their competitors so that they can rise above them. Also, they use it to attack particular competitions and change the final results.
- Hacktivism. Non-governmental organizations and individuals who want to make a point often use such tools to make a noise about their cause. Freedom of speech and ecological causes are common. It could attract media attention, start an international debate and stop the services of the targeted organization.
Consequences of DNS Attacks
Becoming a target of a DNS attack can have a severe negative impact. Let’s examine the most common consequences:
- Data Breaches: One of the most serious consequences of DNS attacks is the potential for data breaches. When attackers successfully manipulate DNS records, they can gain unauthorized access to sensitive information. That means putting personal and financial data at risk, leading to identity theft, financial losses, and reputational damage.
- Business Disruption: Downtime resulting from attacks can have catastrophic effects on businesses. Whether it’s an e-commerce website unable to process transactions or a critical online service experiencing disruptions, the financial damage can be severe. Beyond obvious financial losses, prolonged downtime can have a negative impact on customer trust and loyalty.
- Reputation Damage: DNS attacks not only affect the proper functionality of digital services but can also tear apart an organization’s reputation. Customers, partners, and stakeholders may lose trust in a business’s ability to protect sensitive information, leading to long-term consequences for brand image and market position.
Common Targets of DNS Attacks
Understanding the potential victims of DNS attacks is crucial for implementing robust cybersecurity measures. The following examples are often targeted:
- Enterprises and Organizations: Large corporations and organizations are often targets due to the vast amount of sensitive data they store. DNS attacks can compromise data integrity, leading to financial losses and reputational damage.
- Internet Service Providers (ISPs): ISPs play a key role in managing and directing internet traffic. Attacks on their DNS infrastructure can result in widespread service disruptions, affecting countless users.
- Government Agencies: Governments keep vast amounts of confidential information critical to national security. DNS attacks on government agencies can lead to data breaches and compromise sensitive data.
- E-commerce Platforms: Online retailers are also an attractive target for attacks as they handle numerous financial transactions and store customer details. A successful attack can disrupt services, leading to financial losses and crashing customer trust.
- Critical Infrastructure: Industries such as energy, transportation, and healthcare rely on interconnected systems. DNS attacks on such critical infrastructure can impact public safety and fundamental services.
- Financial Institutions: Financial institutions dealing with sensitive transactions and client data are also often targets of attacks. A successful assault on their DNS can result in phishing attacks, leading to identity theft or fraudulent transactions, causing extreme financial damage.
Signs Your Business Might Be Under a DNS Attack
Detecting a DNS attack early is crucial to mitigating its impact on your business. Here are some key signs that your DNS infrastructure might be under attack:
- Sudden and Unexplained Downtime: If your website or online services experience unexpected outages or are unreachable, it could indicate a Distributed Denial of Service (DDoS) or DNS Flood attack.
- Slow Website Performance: Significant delays in loading your website or services may be a symptom of a DNS flood or an amplification attack overwhelming your servers.
- Unusual DNS Traffic Patterns: A sharp increase in DNS query volume, especially from unfamiliar sources, is a red flag. Analyze DNS logs for any irregularities, such as repetitive queries from the same IP or unexpected geographic sources.
- Frequent User Complaints: Customers may report issues accessing your site, or they might be redirected to malicious or unexpected destinations, signaling a potential DNS cache poisoning attack.
- Suspicious Activity in DNS Logs: Look for anomalies like unexplained query types, unexpected TTL values, or changes to DNS records without authorization.
- Alerts from Security Tools: Security monitoring software often detects abnormal DNS query volumes or traffic patterns. Alerts about unusual activities should not be ignored.
Real-Life Examples of DNS Attacks
DNS attacks are not just theoretical. They are very real and have caused widespread disruption to many businesses and individuals.
A prime example is the Dyn DDoS attack of October 2016, one of the most notorious DNS attacks in history. Cybercriminals leveraged a botnet of compromised IoT devices, flooding Dyn’s DNS infrastructure with massive traffic. This attack disrupted major platforms like Netflix, Twitter, Spotify, and Reddit, affecting millions of users for hours.
Another example is the Kaminsky DNS Cache Poisoning attack in 2008, which exposed a critical flaw in the DNS protocol. This vulnerability allowed attackers to redirect users to malicious websites, posing a significant threat to internet security. The discovery led to the global implementation of DNSSEC as a countermeasure.
In 2020, New Zealand’s stock exchange was targeted by a series of DNS-based DDoS attacks, disrupting trading for several days. It showcased how DNS attacks can harm essential services and cause severe economic damage.
These examples highlight the need for strong DNS security. DNS attacks can target anyone, from corporations to government agencies, stealing data, disrupting services, or causing financial losses. Learning from these cases is key to preventing future threats.
Why DNS Attacks Are Hard to Trace?
One of the biggest challenges with DNS attacks is that they are extremely difficult to trace back to the real attacker. Cybercriminals often use spoofed IP addresses to hide their identity. Instead of sending traffic directly from their own machines, they disguise the source, making it look like the requests are coming from somewhere else.
Many DNS attacks also rely on botnets, which are large networks of infected devices spread across the world. These devices, which can include home computers, smartphones, or even IoT gadgets like cameras, send traffic on behalf of the attacker. With thousands of different sources involved, pinpointing the origin becomes almost impossible.
In addition, some DNS attack methods rely on reflection and amplification. Here, attackers use legitimate DNS servers to send oversized responses to a victim. Because the traffic appears to come from trusted servers, tracing it doesn’t easily reveal the real criminal.
This complexity is why prevention, monitoring, and strong DNS protection are far more effective and important.
Conclusion
It is really important to know about DNS attack types and how to protect us from them so your business experiences fewer shocks. Smooth sail for your business. You don’t want to suffer brand damages, lawsuits that cost millions of dollars or losing clients because of downtime. To avoid them we recommend you take a look of our DDoS protected DNS service, and test our FREE 30-day trial!