Cyber-threats are behind every corner. Recently we wrote about DDoS attacks, and how hackers are using your computer and many connected devices to create a network of bots who can bring down even the best-protected network. Today we will review another danger – DNS spoofing.
DNS spoofing a.k.a. DNS poisoning is so popular that you can find plenty of DNS spoofing tutorials using Kali distribution of Linux, but we are on the good side, and we won’t show you that. We will explain to you why there is such a threat and how you can protect yourself.
Table of Contents
DNS Spoofing – Definition
In 2008, security researcher Dan Kaminsky unveiled a severe flaw in the DNS protocol that left many Internet domains susceptible to poisoning attacks. This disclosure shook the internet community, prompting immediate action and leading to widespread deployment of security patches. Recognizing past vulnerabilities allows us to be vigilant and learn from historical mistakes.
DNS Spoofing appears when the IP address (IPv4 or IPv6) of a domain name is masked and falsified. The information is replaced with a faked one, from a host that has no authority to give it. It occurs and disturbs the normal process of DNS resolution. As a result, the user’s device is connecting with a bogus IP address, and all of the traffic is directed to a malicious website. Additionally, the victim is not able to notice the forgery because the DNS resolution is a process that happens behind the scenes.
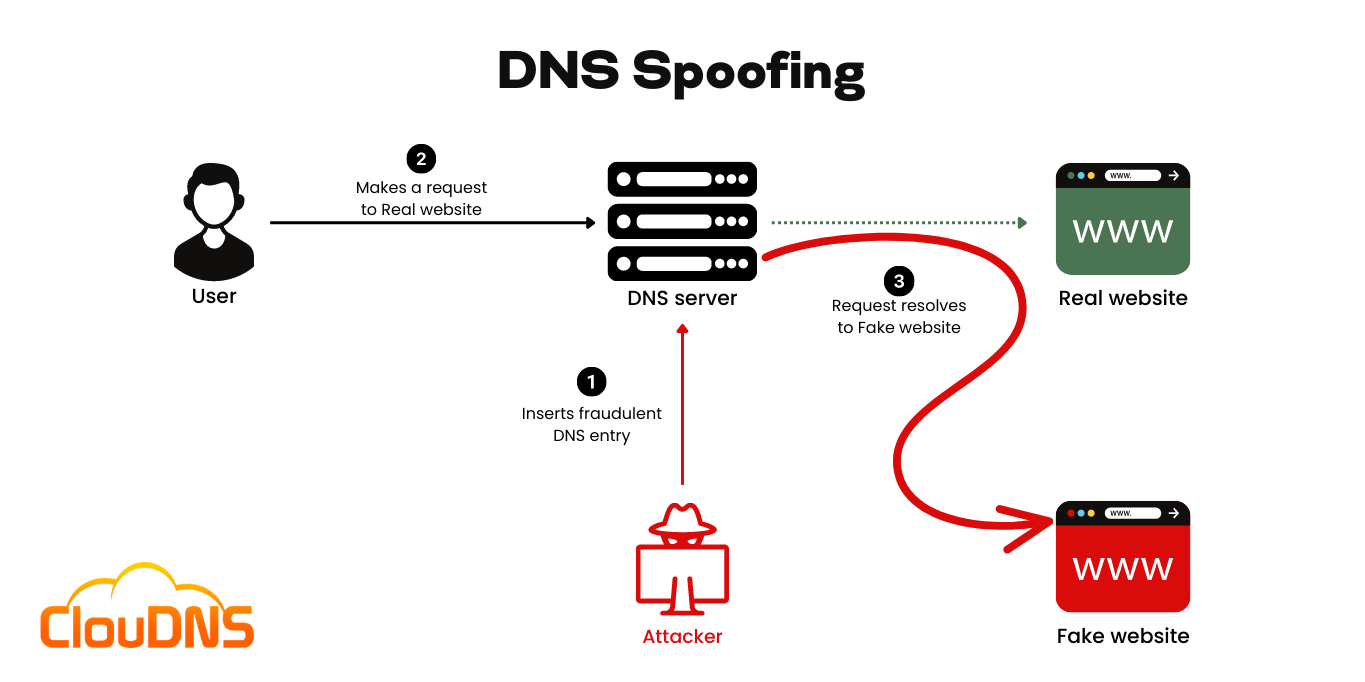
The fake DNS data (DNS records) takes place in the Recursive DNS server cache, which results in the name server answering with a false IP address. Such attacks take advantage of vulnerabilities in name servers and shift the traffic towards fake web pages. Those fake websites are visually very similar to the real ones, and people don’t even understand the difference. In this process, personal data can be stolen.
As we mention above, the Recursive DNS server has an essential role in the DNS resolution process. Let’s explain a little bit more about it. Here are two functions that you should be familiar with:
DNS caching
To save time and better divide the load, in the DNS there are recursive DNS servers. They have a cache, local saved information about the domains that temporarily stays in them.
Forwarding
Even a caching name server does not necessarily perform the complete recursive lookup itself. Instead, it can forward some or all of the queries that are not satisfied from its cache to another caching name server, commonly referred to as a forwarder.
Experience Industry-Leading DNS Speed with ClouDNS!
Ready for ultra-fast DNS service? Click to register and see the difference!
Methods of DNS Spoofing
There are various different methods of DNS Spoofing. Here are some of the most popular ones:
Spoofing the DNS responses
This method is a form of a Man-in-the-Middle (MITM) attack. In this one, the attacker is guessing the manner in which the DNS generates its query ID and sends a fake response with the IP address he/she wants.
In the majority of cases, the cybercriminal pretends to be the victim’s DNS server and sends malicious responses. The chance for initiating such a type of attack is based on the fact that DNS traffic operates with the User Datagram Protocol (UDP). That way, it is not possible for the victim to confirm the authenticity of the DNS response.
DNS cache poisoning
DNS cache poisoning or also known just “cache poisoning,” is another cyber attack that cybercriminals commonly initiate. It involves placing a bogus IP address in the cache memory of the devices of the users. That way, the target victim device is going to lead the user to that bogus IP address automatically. It includes sending to the DNS servers wrong mapping information with high TTL. The information is saved for a long time so the server can give the fake answer for a long time.
Learn everything about the DNS Cache!
Moreover, each further DNS request to the DNS servers with this cached, malicious information is going to direct to the bogus IP address. Such a threat is going to remain until the entry is pulled from the DNS cache. However, there is a security mechanism called DNSSEC which can be implemented to improve the protection of your DNS.
DNS Hijacking
DNS Hijacking is one of the most complex DNS attacks out there. The cybercriminal hijacks a legitimate DNS server and takes control of it. Then, he or she makes some modifications to the DNS information (DNS records). That way, the fake DNS data pushes every user who reaches that website’s IP address to get sent to the falsified website. That is why encryption is especially important for the overall protection of your information.
Example of DNS Spoofing
Most commonly, attackers utilize premade tools to complete a DNS Spoofing attack. Typically, it is performed in any location with connected devices, yet the main targets are locations with free public Wi-Fi. They are usually poorly secured and misconfigured. That gives the cybercriminal a great opportunity to complete the malicious attempt. Therefore, it is best if you consider using only secure Wi-Fi networks.
Here is an example of DNS Spoofing and the basic steps that the cybercriminal completes:
- The attacker uses arpspoof to trick the target device of the user and point it to the attacker’s machine. So, when the user writes the domain name into the browser, it is going to be misguided. As a result, the cache of the user device is poisoned with forged data.
- The attacker creates a DNS server on a device under his or her control. That way, the attack proceeds by rewriting the DNS records for the target domains.
- The cybercriminal established a website that imitates a legitimate one on a local malicious device. Despite the fact it looks and feels legit, such a website is created for phishing purposes.
- When the victim tries to establish a connection and open such a website, it receives the IP address provided by the attacker’s DNS server. As a result, the victim opens the phishing website instead of the legitimate one.
- Lastly, the threat actors steal information from their victims on the network by tricking them. Commonly, that is performed by them entering their sensitive information into the fake website pages.
Suggested article: Linux Host command, troubleshot your DNS
The Impact of DNS Spoofing: Consequences and Risks
- Misdirection to malicious websites: Users are directed to fraudulent sites designed to steal sensitive information, often indistinguishable from genuine ones.
- Data theft and privacy breaches: Attackers can capture personal details and login credentials, leading to identity theft and potential financial repercussions.
- Spread of malware: Victims are at risk of malware infections when they’re redirected to malicious sites, compromising their devices.
- Phishing attacks: By mimicking genuine domains, attackers craft convincing phishing attempts, duping victims into sharing confidential data.
- Loss of trust and reputation damage: For businesses, a DNS spoofing incident can result in significant reputational harm and a decline in customer trust.
- Financial consequences: Both individuals and businesses might face direct financial losses, coupled with the costs of damage control and cybersecurity enhancements post-incident.
Common Vulnerabilities that Lead to DNS Spoofing Attacks
DNS spoofing attacks often exploit various vulnerabilities within the DNS infrastructure. One primary weakness is unsecured DNS servers, which become easy targets for attackers when left with default settings. The absence of DNSSEC (Domain Name System Security Extensions) is another critical vulnerability. Without it, DNS responses cannot be verified for authenticity, leaving them open to manipulation.
Weak or misconfigured DNS cache settings also pose significant risks, as they can be poisoned with malicious records, redirecting users to fraudulent websites. Insecure network configurations, especially on public Wi-Fi, further expose systems to man-in-the-middle attacks. Outdated software on DNS servers and related devices makes it easier for attackers to exploit known vulnerabilities.
The lack of monitoring allows spoofing attacks to go unnoticed, causing prolonged damage. Poorly configured firewalls, access controls, and insecure DNS forwarding also contribute to the risk. Finally, human errors and social engineering tactics often play a role in successful DNS spoofing attacks.
Addressing these vulnerabilities through regular updates, security audits, and robust configurations is essential to prevent DNS spoofing and secure DNS operations.
How to protect from DNS spoofing?
There are few different things that you can do to protect from those attacks:
- DNS over HTTPS (DoH) and DNS over TLS (DoT): These protocols encrypt your DNS requests, ensuring that attackers can’t view or modify them.
Understanding DoT and DoH - Use DNSSEC – Domain Name System Security Extensions checks the data authenticity with digitally signed DNS records.
- Internal DNS Servers: Establishing a secure internal DNS server setup can add an extra layer of protection. Ensure regular security audits to keep it foolproof.
- Implement DNS filtering. It will block malicious IPs or domains from connecting to your system.
- Use IPSec – IPSec uses encryption to secure communication over IP networks, enhancing data flow between hosts and networks.
- Detection mechanisms. You can use monitoring software to detect it. Using such a program, you can be sure that it will alert you if it detects some suspicious traffic which can be DNS spoofing.
- Always use a secure connection. Use encryption via SSL or TLS to verify the certificate of the website you want to visit.
What is an SSL certificate? - Employee Training: Periodic training sessions can help employees recognize and report potential cyber threats, reducing the chance of a successful attack.
Comparing DNS Spoofing with ARP Spoofing
When discussing cybersecurity threats that involve redirecting traffic, two techniques often come up: DNS spoofing and ARP spoofing. While both are forms of deception in network communications, they occur at different layers of the OSI model and have distinct attack vectors and consequences.
- DNS spoofing takes place at the application layer (Layer 7) and involves redirecting a user to a fraudulent IP address by corrupting DNS data. This is typically done by injecting false records into a DNS cache or by intercepting DNS responses.
- ARP spoofing, on the other hand, occurs at the data link layer (Layer 2). It involves sending fake Address Resolution Protocol (ARP) messages on a local network to associate the attacker’s MAC address with the IP address of another host, typically a gateway or server. This allows the attacker to intercept, modify, or block traffic between two devices – commonly used in man-in-the-middle attacks.
Both attacks can result in traffic redirection, credential theft, and session hijacking, but their execution and scope differ. DNS spoofing can affect users globally if a public DNS resolver is compromised, while ARP spoofing typically requires access to the same local network as the target.
Conclusion
We should be cautious where we go on the internet and what emails we are opening. Even the slightest difference, like the missing of the SSL certificate, should immediately trigger us to double check the website we want to visit.