Without Domain Name System (DNS), there is no Internet. It is the key ingredient that makes domain resolving possible. We use DNS to access sites, send and receive emails when we use applications. All-day, every day!
Table of Contents
Domain Name System – DNS
DNS or a Domain Name System is an amazing technology. You can see DNS as a hierarchy system of domains/hostnames and IP addresses. It helps us open internet addresses without a hustle. We easily write the domain name and the DNS has the job to find the IP of the domain we wrote. Just like the phone book on your mobile phone, you need to find Mike, so you write “Mike”, and you don’t need to remember his actual number, great isn’t it?
DNS is an essential part of the Internet. It manages to translate all the inquiries into IP addresses, and like this, it can identify different devices that are connected to the network.
Apart from translating hostnames to IP addresses (A and AAAA DNS records), DNS also has many different functions like defining port in use, connecting services to domains, authentication of emails, and many more. There are 50+ types of DNS records with different functionality.
Why do we need the Domain Name System (DNS), and why is it important?
The Domain Name System is a fundamental component of the Internet infrastructure, playing an essential role in ensuring the smooth operation of online services and communication. DNS serves for:
- Matching hostnames to IP addresses: DNS allows users to access websites using memorable domain names instead of complex IP addresses, improving usability and accessibility.
- Pointing services: It enables organizations to map domain names to specific services, such as web servers, email servers, FTP servers and more.
- Directing messages to mail services: DNS also plays a crucial role in email delivery by mapping mail server addresses (MX records) to domain names. This ensures that emails are routed correctly to their intended recipients.
- Authentication and validation of emails and different services: It supports various protocols, such as SPF, DKIM, and DMARC, which authenticate and validate email senders and prevent spam and phishing attacks.
- Creating VPN: DNS can be used to set up Virtual Private Networks (VPNs) by resolving domain names to internal IP addresses and ensuring secure remote access to corporate resources.
- Creating a Content Delivery Network: DNS powers Content Delivery Networks (CDNs) by routing requests to geographically distributed servers, optimizing content delivery and enhancing user experience.
- Load balancing: DNS-based load balancing distributes traffic across multiple servers, improving scalability, resilience, and performance.
- Increase your uptime: Effective DNS management strategies, such as redundant server setups and optimized configurations, contribute to increased uptime.
Ready for ultra-fast DNS service? Click to register and see the difference!Experience Industry-Leading DNS Speed with ClouDNS!
DNS history
Before the Internet, there were different networks like ARPANET, SATNET, and many packet radio ones. The problem was that there was not a single united network. There was a need to solve this problem, and the solution was the Domain Name System (DNS).
The person who got the task to create it was Paul Mockapetris. His team needed to find a way to have IP addresses and hostnames aligned.
A centralized file called HOSTS.TXT matched the first existing sites to IP addresses, but this was not a solution that could handle millions of sites.
After several years of work, in 1983, the DNS was created and joined the Internet Standards of Internet Engineering Task Force in 1986. The founding documents of it were RFC 1034 and the second RFC 1035. There you can find information about the protocol, its functionality, and data types.
A later update of DNS allowed dynamic zone transfers (IXFR) and the use of NOTIFY. The NOTIFY mechanism gave the Primary DNS servers the power to “notify” the Secondary about the changes in the DNS records.
Now the Secondary DNS servers could update when a change occurs in the Primary and get only the change.
And another critical moment was the creation of the DNSSEC and its version from 1999 (RFC 2535). It is a security layer that defends the DNS from poison attacks.
Here you can read more about the History of DNS.
Components of DNS. What does DNS include?
The Domain Name System has several essential components, each playing a crucial role in its operation:
- Domain namespace. It is a tree-like hierarchy structure that divides hostnames into smaller pieces called domains. They are further divided into more categories: top-level domains, second-level domains, and subdomains.
- DNS servers. These servers handle the resolution of domain names to IP addresses. They include authoritative servers with the original DNS records, recursive servers that cache and resolve queries, root name servers that direct queries to TLD servers, and TLD servers that manage second-level domains.
- DNS query. Each request comes from a device that demands a DNS record. It is a question that runs from one recursive server to another in search of the answer.
- DNS records. Domain name system keeps information in so-called DNS records. They are text documents with various purposes like A Record, SPF record, CNAME record, etc.
DNS server types
DNS servers play different roles in the process of resolving domain names. Here are the primary types of DNS servers:
- Recursive DNS servers: These servers handle queries from clients and perform the necessary lookups to resolve domain names into IP addresses. They can cache results to speed up future queries.
- Root Name servers: Root servers are at the top of the DNS hierarchy. They respond to queries for records in the root zone and direct them to the appropriate Top-Level Domain (TLD) servers.
- TLD Name servers: These servers manage the DNS records for domains under a specific top-level domain, such as .com, .org, or .net. They direct queries to the authoritative servers for the requested domain.
- Authoritative DNS servers: These servers store the DNS records for a domain. They provide answers to queries about domains they are responsible for, delivering the most accurate information.
How does the Domain Name System work? Example:
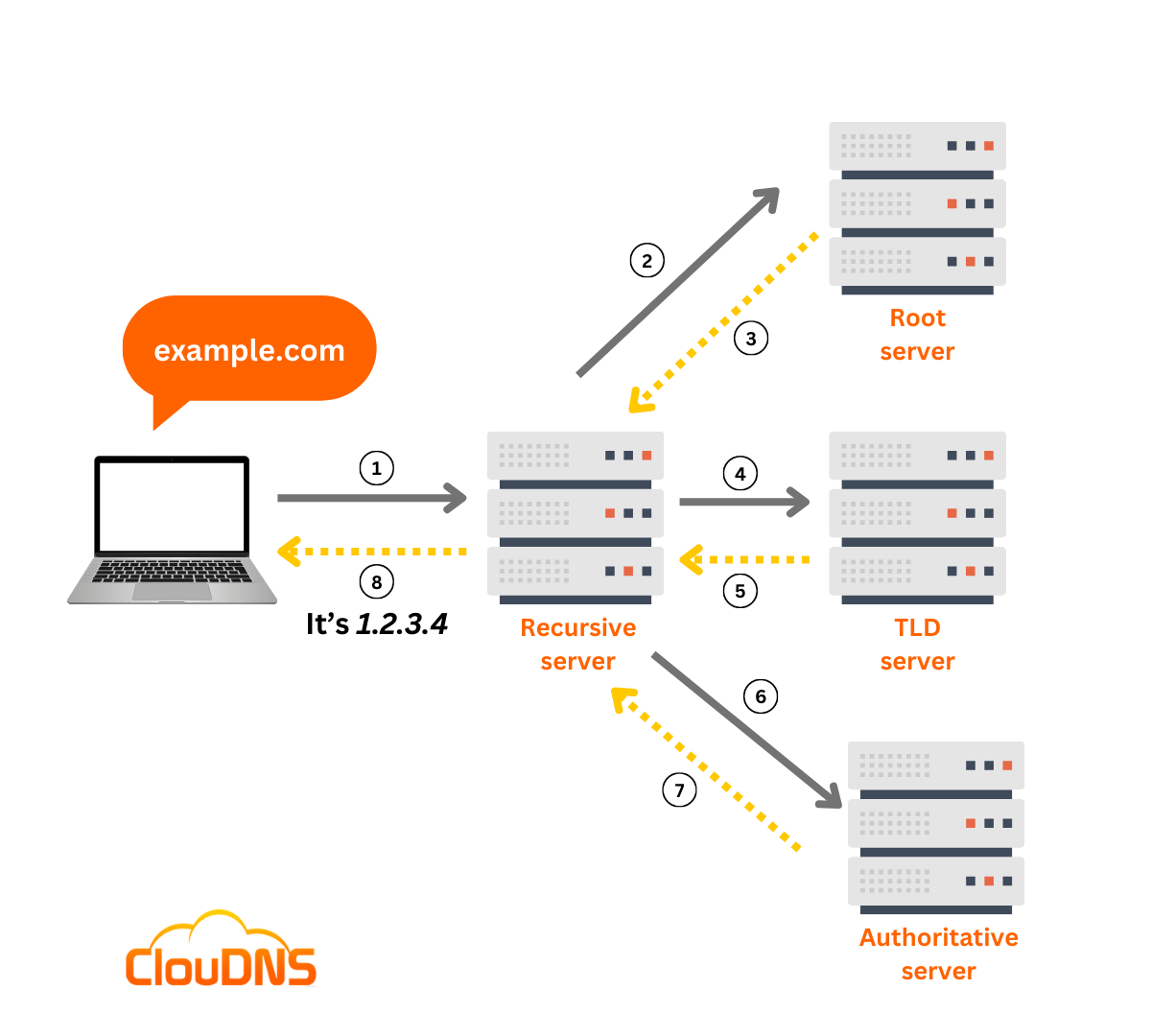
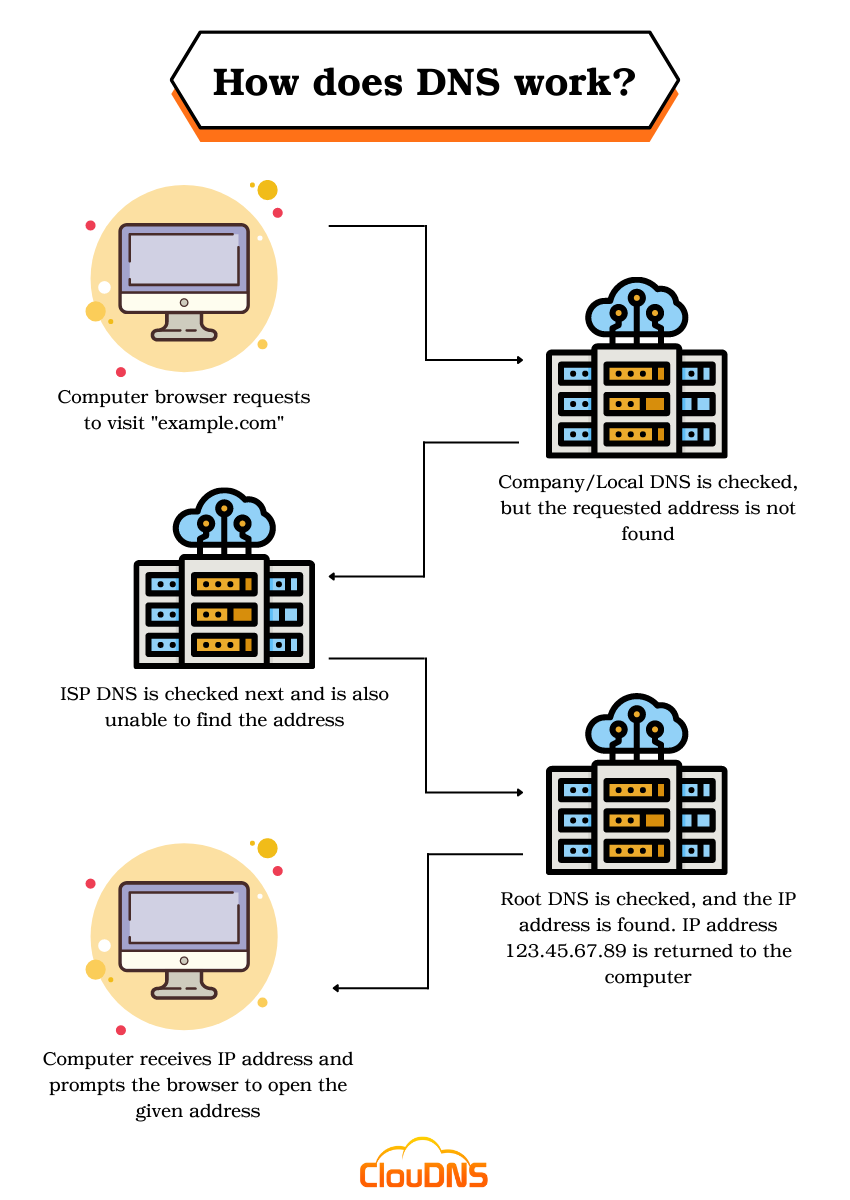
Let’s explain a little bit more about how DNS actually works. The process has the following steps:
1. Information request
You want to visit our website and you know the domain name. You write it in your browser, and the first thing it does is to check for local cache if you have visited it before, if not it will do a DNS query to find the answer.
2. Recursive DNS servers
If you haven’t visited the page before, your computer will search the answer with your internet provider’s recursive DNS servers. They have cache too so you can get the result from there. If they don’t, they will need to search the information for you in another place.
3. Root name servers
Your query can travel a long way. The next step is the name servers. They are like intermediates; they don’t know the answer, but they know where to find it.
4. Top-Level Domain (TLD) name servers
The name servers will read from right to left and direct you to the Top Top-Level Domain (TLD) name servers for the extension (.com or another). These TLD servers will lead you finally to the servers which have the right information.
5. Authoritative DNS servers
These DNS servers check the DNS records for the information. There are different records, for example, we want to know the IP address for a website, so our request is Address Record (A).
Premium Authority DNS service - Try for free
6. Retrieve the record
The recursive server gets the A record for the website we want from the authoritative name servers and stores it on its local cache. If somebody else needs the host record for the same site, the information will be already there, and it won’t need to pass through all these steps. All this data has an expiration date. This way, the users will get up to date information.
7. The final answer
Now that the recursive server has the A record it sends it to your computer. The PC will save the record, read the IP and pass the information to your browser. The browser makes the connection to the web server, and it is finally possible for you to see the website.
Commonly used DNS records
The DNS records represent instructions and information about a specific domain name. A DNS query is initiated to find such information, and a different DNS record could be pursued depending on the user, query, or application.
There are a lot of different DNS record types, and each of them serves a precise purpose. Here are some of the most commonly used DNS records:
- SOA record – The SOA stands for Start Of Authority. It is one of the fundamental DNS records which describes the origin of the authoritative DNS zone. Additionally, it holds important details about the zone, including information about the primary name server, the domain administrator’s email address, the domain serial number, and details regarding zone transfers.
- A record – The A simply means address. This record contains the IP address of a domain. It is important to mention that A records are responsible for IPv4 addresses. In case you need a record for your IPv6 address, then you should use the AAAA record instead. In most cases, websites have a single A record. However, some sites are more significant and hold more than one. That is very beneficial for load balancing and handling heavy traffic.
- NS record – This is another fundamental DNS record that indicates which is the responsible authoritative server for keeping all related data for a particular domain. There are cases when domains have primary and secondary (backup) name servers for better reliability, then multiple NS records are required for directing DNS queries to them.
- CNAME record – A Canonical Name record is a very helpful type of DNS record that points one hostname to another hostname. It is typically utilized to direct a subdomain, like www, or mail to the domain. Yet, you should be careful because it can’t coexist with other DNS records.
- TXT record – This record allows the DNS administrator to include text instructions related to their domain name. TXT records are commonly used for verifying domain ownership, securing your emails, and protecting against email spam.
- SPF record – The Sender Policy Framework record is a TXT DNS record type that specifies which servers have permission to send emails on your domain’s behalf. It is crucial if you want to stop criminals from spoofing your domain.
How does the Domain Name System affects the web performance?
Recursive DNS servers are able to store the DNS data (like A records and IP addresses) received from DNS queries in their DNS cache for a limited amount of time. That way, the servers are capable of providing quick replies if requests for the same IP address appear. For that reason, caching DNS information is very efficient.
When multiple users request to access the same website, the local DNS server would have to complete the entire DNS resolution process just once. Afterward, it will answer the rest of the requests with the information in its DNS cache.
As we mentioned, the DNS data is available only for a specific amount of time, determined by the TTL (Time-To-Live) value. Administrators have the responsibility to set it, and it could be different depending on their preferences. Longer TTL helps decrease the load on the Authoritative DNS servers. On the other hand, shorter TTL will guarantee more accurate answers.
Suggested article: What web performance monitoring is?
DNS server not responding? How to fix it?
When you encounter the message “DNS Server Not Responding,” it means your device is unable to contact the DNS server to resolve the domain name you are trying to access. This issue can arise from various causes:
- Network Connectivity Issues: There might be problems with your internet connection or the network you are using.
- DNS Server Problems: The DNS server you are trying to reach may be down or experiencing high traffic, making it unresponsive.
- Incorrect DNS Settings: Your device’s DNS settings might be configured incorrectly, preventing it from communicating with the DNS server.
- Firewall or Security Software: Sometimes, firewall or security software on your device can block DNS traffic.
To resolve this issue, try these troubleshooting steps: switch to a different browser or device to see if the problem persists, check your network connection and restart your router, temporarily disable your antivirus software and firewall, and ensure no conflicting secondary connections or peer-to-peer features are active. Additionally, update your network adapter drivers, flush your DNS cache using Command Prompt, and consider changing your DNS server settings to a reliable service. Disabling IPv6 in your network settings may also help.
DNS SECURITY
Over time, cybercriminals found vulnerabilities in the Domain Name System (DNS) and managed to use them to their own advantage. The most common threat is called DNS spoofing (DNS poisoning), where falsified data is distributed to the Recursive DNS servers. Usually, the false information directs user requests to a source pretending to be the Authoritative DNS server. So, as a result, the requests are typically directed to a fake website.
Criminals use tricky titles and aim to convince users that the website is genuine, so they can gain access to the user’s personal details. Sometimes, for instance, they substitute a character in the domain name with a similar-looking character, like replacing the letter l with the number 1. If the user doesn’t notice the difference, the risk of becoming a victim of a phishing attack is relatively high.
The best option for boosting your DNS security and minimizing the risk of becoming a victim of DNS spoofing (DNS poisoning) is to implement DNSSEC (DNS Security Extensions). With it, the DNS data (DNS records) is signed cryptographically. That way, its integrity and authenticity are guaranteed. Other security measures for mitigating such threats are DNS-over-HTTPS (DoH) and DNS-over-TLS (DoT), which encrypt DNS queries and responses, protecting them from eavesdropping and tampering.
Conclusion
The Domain Name System is a fundamental pillar of the Internet, enabling seamless access to websites and services by translating human-readable domain names into IP addresses. It is a long process, but actually, it takes fractions of a second. It can be even faster if you use reliable DNS servers from ClouDNS. Check our DNS services and choose the one that best suits you. With continuous advancements and robust security measures like DNSSEC, DNS remains a reliable and secure backbone of the Internet. For businesses and individuals alike, understanding and optimizing DNS can lead to improved web performance, enhanced security, and a better overall user experience.
30-day Free Trial for Premium Anycast DNS hosting




This is my first time visit aat herde and i am truly
impressed to read all at onne place.
That was an amazing article about the domain name, it helps me in understanding what domain name is.
Nice blog author. Thank you. Keep it up.