DNS Tunneling attack turns the Domain Name System (DNS), a highly trusted and widely used system on the Internet, into a weapon for cybercriminals. This type of attack takes advantage of this protocol and achieves to sneak malicious traffic through the defenses of the organization (victim).
Cybercriminals are using malicious domain names and DNS servers to bypass the protection and complete data exfiltration.
Before we jump into explaining what the DNS tunneling attack is and how it works, let’s talk a little bit more about what DNS is.
Table of Contents
Domain Name System – explained
The Domain Name System, or just for short DNS, is a global naming database. Thanks to it, we are able to use the Internet, as we do in the present day. Its purpose is to translate human-readable domain names, such as example.net, into their corresponding machine-friendly IP addresses, such as 123.45.67.89. That way, regular users are not required to remember long and difficult numbers. Instead, people are easily memorizing domain names, and they can use them to reach and explore their favorite news, sports, or another website.
A lot of services rely on the large number of DNS translation queries that appear constantly. For that reason, DNS traffic is widely used and trusted. Due to the fact that DNS was not invented to transfer data packets but only for name resolution was not viewed as a threat to malicious communications and data exfiltration. Yet, DNS is not just a translation instrument for domain names. DNS queries can also transfer tiny portions of data between two devices, systems, and servers. The bad news is that this makes DNS a potential vector for attacks.
Unfortunately, the majority of organizations do not analyze the DNS packets for malicious activity frequently. Instead, they mainly concentrate on analyzing web or email traffic where they consider a possible attack could appear. The truth is that each endpoint should be under detailed monitoring for preventing DNS tunneling attacks.
DNS Tunneling – what do you have to know?
DNS Tunneling attack is a very popular cyber threat because it is very difficult to detect. It is used to route the DNS requests to a server controlled by the attacker and provides them with a covert command and control channel and data exfiltration path.
Typically, DNS tunneling involves data payloads that are added to the target DNS server. Additionally, they are implemented for gaining control of a remote server and applications. Moreover, for the purpose of this attack, the compromised system should be connected to an external network to achieve access to an internal DNS server with network access. Cybercriminals control a server that operates as an authoritative server and a domain name to complete the server-side tunneling and data payload executable programs.
5 DNS Attacks Types that could affect you
DNS Tunneling History
DNS tunneling history is highly related to the evolution of cybersecurity threats. It appeared as a technique for bypassing network restrictions and avoiding detection. At first, it was used for legitimate purposes like bypassing restrictive networks or anonymous online activity. However, DNS tunneling slowly became popular among malicious actors as a secret communication channel for data exfiltration and command-and-control purposes. The first examples of this attack appeared in the early 2000s and were often associated with malware propagation. Over the years, the attackers become more sophisticated, and their techniques have evolved. That forced cybersecurity specialists to develop advanced monitoring and prevention mechanisms to protect against it.With the rise of digital platforms and streaming services, cybersecurity threats also impact industries like broadcasting and content creation. For instance, businesses using a TV channel maker to set up their own streaming platforms must ensure robust security measures to protect against potential cyber threats, including DNS tunneling attacks.
Experience Industry-Leading DNS Speed with ClouDNS!
Ready for ultra-fast DNS service? Click to register and see the difference!
How does it work?
DNS tunneling attack takes advantage of the DNS protocol and achieves tunneling malware or data through a client-server model. Let’s explain how this attack actually works.
It all starts when a user downloads malware or the cybercriminal manages to exploit a vulnerability of the compromised device to transfer a malicious payload. In most cases, the cybercriminal wants to keep a connection with the compromised device, meaning to have the opportunity to run commands on the target device or exfiltrate data. Therefore, the attacker can set a command-and-control (C2) connection. Such traffic should be able to pass via different network perimeter security measures, plus it should avoid detection until it crosses the target network.
For that reason, DNS is a suitable option for setting up the tunnel. That is a common term in cybersecurity which stands for a protocol connection that carries a payload that includes data (commands) and passes through perimeter security measures. That way, the DNS tunneling attack manages to hide information within DNS queries and send them to a server controlled by the cybercriminal. The DNS traffic passes freely through perimeter security measures, such as firewalls. For the purpose of setting the DNS tunnel, the cybercriminal registers a domain name and configures an authoritative name server under their control.
Then the malware or payload on the compromised device initiates a DNS query for a subdomain that defines an encoded communication. The Recursive DNS server (DNS resolver) obtains the DNS query and routes it to the attacker’s server. The server responds with malicious DNS data containing data (command) back to the compromised device. This entire process can evade detection, making vulnerabilities like these a significant threat. Conducting regular vulnerability assessments can help identify weak points that attackers may exploit, enhancing overall defenses against such sophisticated attacks.
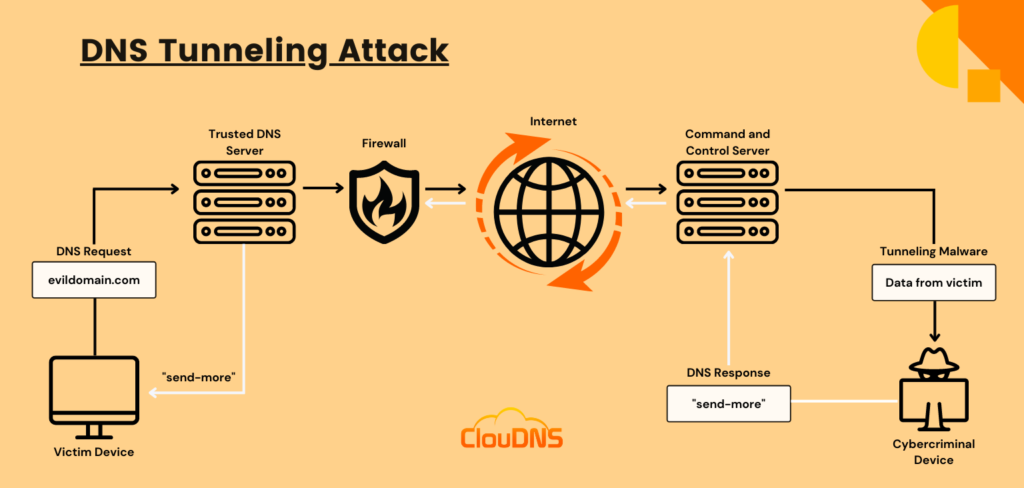
Let’s break the DNS Tunneling attack into the following steps:
- The cybercriminal registers a domain and points it to the server under its control. There is installed tunneling malware software.
- The cybercriminal infects a device with malware, penetrating the victim’s firewall. DNS requests don’t have restrictions for passing in and out of the firewall.
- The Recursive DNS server (DNS resolver) requests the IP address through root and top-level domain servers.
- Then the DNS resolver routes the DNS query back to the authoritative DNS server, which is controlled by the attacker and contains the tunneling software.
- The connection between the cybercriminal and the target is created without any notice.
Why do Attackers Use DNS Tunneling?
Attackers use DNS tunneling to exploit the widespread and often under-monitored nature of DNS traffic. This attack allows them to secretly transmit data between a compromised system and a command-and-control server. Since DNS queries and responses are generally trusted and rarely scrutinized, this technique can easily bypass firewalls and other security measures. DNS tunneling allows attackers to maintain persistent access, execute remote commands, and exfiltrate sensitive data without detection. The global reach and minimal inspection of DNS make it an ideal medium for hidden communication and data transfer.
Detecting DNS Tunneling
There are several techniques that can help you detect a DNS tunneling attack. However, we can distinguish them into two main categories – payload analysis and traffic analysis.
Payload analysis – The DNS payload for one or more requests and responses is going to be examined for tunnel signs.
- Examining the size of the request and answer. Typically, DNS tunneling utilities are pushing to place as much data into the requests and answers as possible. Therefore, the tunneling requests are more likely to have long labels. For instance, there are up to 63 symbols and, in general, long names – up to 255 symbols.
- Disorder of hostnames. DNS names that are authentic commonly contain dictionary words and have some kind of meaning. Names that are encoded are usually out of any order, plus they are even using a set with more characters.
- Statistical Examination. You can detect tunneling by checking the specific character staff of the DNS names. DNS names that are authentic commonly contain fewer numbers. On the other hand, encoded names tend to have a lot of numbers. Examining the percentage of numerical characters in domain names and examining the percentage of the length of the Longest Meaningful Substring (LMS) could also help you.
- Uncommon DNS Record Types. You can check for DNS records that are not usually implemented by a regular client. For example, you can examine the TXT records.
- Violating a policy. In case a policy directs every DNS lookup to pass through an internal DNS server, violations of that policy may be employed as a detection technique.
- Special Signatures. You can use a special signature to examine precise attributes in a DNS header. Then scan for particular content in the payload.
Traffic analysis – The traffic is under examination over time.
- Volume of DNS traffic per IP address. A simple and easy to accomplish technique is to check the specific amount of DNS traffic that is coming from a particular client IP address.
- Volume of DNS traffic per domain. Another method that is very easy and basic is by checking for massive amounts of traffic towards a precise domain name. DNS tunnel utilities are typically established to tunnel the data by involving a precise domain name. Therefore, all of the tunneled traffic is going to be that exact domain name.
- The number of hostnames per domain. DNS tunneling utilities ask for an individual hostname on every request. That effects by increasing the number unusually compared to a normal authentic domain name.
- Geographic location of DNS server. You can check for a massive amount of DNS traffic that is directed to geographical areas where you don’t offer your services or products.
- The history of a domain. You can examine when an A record (AAAA record) or NS record was created and added to a domain name. That technique is very useful for detecting domain names that are utilized for malicious criminal actions.
Source: GIAC Certifications
Protection against DNS Tunneling attacks
DNS is a crucial service, so it is going to be a problem if you are considering blocking it. Thus, protection against a DNS Tunneling attack involves several actions that are going to help you prevent such an attack.
- You should keep a closer look and track of questionable IP addresses and domain names that are from non familiar sources.
- You can set all of the internal clients to direct their DNS requests (DNS queries) to an internal DNS server. That way, you can filter potential malicious domains.
- It is very important to stay watchful for any suspicious domain names, and it is best if you always monitor the DNS traffic. That will help reduce the chance for a DNS tunneling attack to appear.
- Establish a DNS firewall for recognizing and stopping any hacker intrusion.
- A real-time DNS solution that is able to detect uncommon DNS queries and unusual traffic patterns on the DNS server is another excellent option.
Using DNS Monitoring against DNS tunneling
DNS Monitoring can be crucial in mitigating the risks of DNS tunneling by providing real-time visibility into DNS traffic patterns and behavior. By constantly analyzing DNS queries and responses, DNS monitoring can detect anomalies and suspicious activities that indicate tunneling attempts. This proactive monitoring allows organizations to quickly identify and respond to potential threats, such as secret data exfiltration and command and control communications before they escalate. Additionally, the ClouDNS Monitoring service offers different alerting mechanisms that notify administrators of any unusual DNS activities. That way, they can take timely action to investigate and block malicious traffic. Thanks to the extensive monitoring capabilities, organizations can strengthen their DNS infrastructure and improve their ability to defend against different threats, including DNS tunneling.
Risks and Impact of DNS Tunneling
DNS tunneling attack poses several significant risks to organizations:
- Data Breaches: Attackers can exfiltrate sensitive information, including personal data, intellectual property, and financial records.
- Unauthorized Access: Allows attackers to maintain hidden, persistent access to compromised systems.
- Operational Disruption: Enables the execution of remote commands, potentially leading to system malfunctions or downtime.
- Financial Loss: Costs associated with data loss, various fines, and restoration efforts can be significant.
- Reputational Damage: Public exposure of breaches can harm an organization’s reputation, leading to loss of customer trust and business.
- Detection Challenges: The nature of DNS tunneling makes it difficult to detect and mitigate, increasing the potential for long-term undetected exploitation.
Examples and Cases
Over the years, several famous examples of DNS tunneling have highlighted its power as a cyber threat:
- Sea Turtle Campaign (2019)
The Sea Turtle campaign in 2019 highlighted the advanced tactics of state-sponsored cyber espionage. This campaign targeted domain registrars, telecommunications firms, and government entities to compromise their DNS records. Attackers manipulated DNS records to redirect legitimate traffic to malicious servers under their control. DNS tunneling played a key role in allowing the attackers to maintain persistent access, exfiltrate sensitive information, and establish C2 channels while remaining undetected.
- SUNBURST Malware (2020)
The SUNBURST malware, a significant component of the SolarWinds supply chain attack in late 2020, demonstrated the sophistication of modern cyber threats. SUNBURST used DNS tunneling as one of its communication methods to establish contact with its C2 infrastructure. By embedding communication within DNS queries and responses, the malware achieved secret data exchange with remote servers. That way, attackers were able to exfiltrate stolen data and receive further instructions while avoiding detection by security measures focused on more traditional communication protocols.
- UDPoS Malware (2015)
The UDPoS malware, discovered in 2015, demonstrated a variation of DNS tunneling where attackers used User Datagram Protocol (UDP) packets to exfiltrate stolen credit card data. The malware encoded the stolen information into DNS queries, which were then transmitted over UDP to avoid detection by traditional network security controls. This technique allowed the attackers to bypass network monitoring tools that usually focus on Transmission Control Protocol (TCP) traffic.
TCP Monitoring vs. UDP Monitoring
Best Practices
Implementing best practices is essential for reducing the risk of DNS tunneling attacks and strengthening overall DNS security.
Start by executing centralized DNS resolution, and configure all internal devices to use designated internal DNS servers only. This allows you to monitor and filter outgoing DNS traffic effectively.
Deploy DNS filtering and threat intelligence tools to block known malicious domains and detect abnormal query patterns in real time. Regularly update DNS firewall rules to reflect emerging threats and ensure your DNS servers are securely configured with minimal exposure to the public internet.
Implement network segmentation to limit the lateral movement of threats within your infrastructure. Modify access and give users and devices the permissions they really need. That way, if something goes wrong, the damage is restricted.
Finally, don’t forget about training your team. Help employees understand how to spot phishing emails and avoid downloading suspicious files. Many attacks start with someone accidentally installing malware.
By following these simple best practices, even small businesses can greatly reduce the risk of DNS tunneling and improve their overall cybersecurity.
Conclusion
DNS tunneling is a severe cyber threat. It could lead to massive negative consequences. This is because the cybercriminal uses the tunnel for malicious ends, like exfiltrating information. In addition, there is no direct association between the cybercriminal and the target. That makes it hard to detect the attacker’s attempt.