The evolution and the usage of smartphones, laptops, tablets, and other devices demand versatility. As a result, the world is more dynamic than ever, and mobile usage makes IMAP very popular. In today’s article, we will explain what IMAP actually means and clarify how it works in detail. So, without any further ado, let’s start!
Table of Contents
IMAP definition
Internet Message Access Protocol, also known as IMAP, is a popular application layer protocol that serves for receiving email messages from a mail server over a TCP/IP connection (Internet). It was created back in 1986 by Mark Crispin as a remote access mailbox protocol. Now, the latest version is IMAP4. Moreover, it is very beneficial and the most common protocol for retrieving emails.
Brief History of IMAP
IMAP, or Internet Message Access Protocol, is an email protocol that dates back to the early 1980s. It was developed as an alternative to the more traditional Post Office Protocol (POP). Unlike POP, which was designed for downloading emails to a single device and then removing them from the server, IMAP was developed with the aim of synchronizing emails across multiple devices while keeping them on the server.
IMAP’s invention was a game-changer. It allowed users to access their emails anytime, anywhere, and on any device with an internet connection. Moreover, it let them maintain a consistent and updated view of their mailbox. Over the years, IMAP has seen several revisions and enhancements, making it a reliable and universal choice for modern email management.
Experience Industry-Leading DNS Speed with ClouDNS!
Ready for ultra-fast DNS service? Click to register and see the difference!
How does it work?
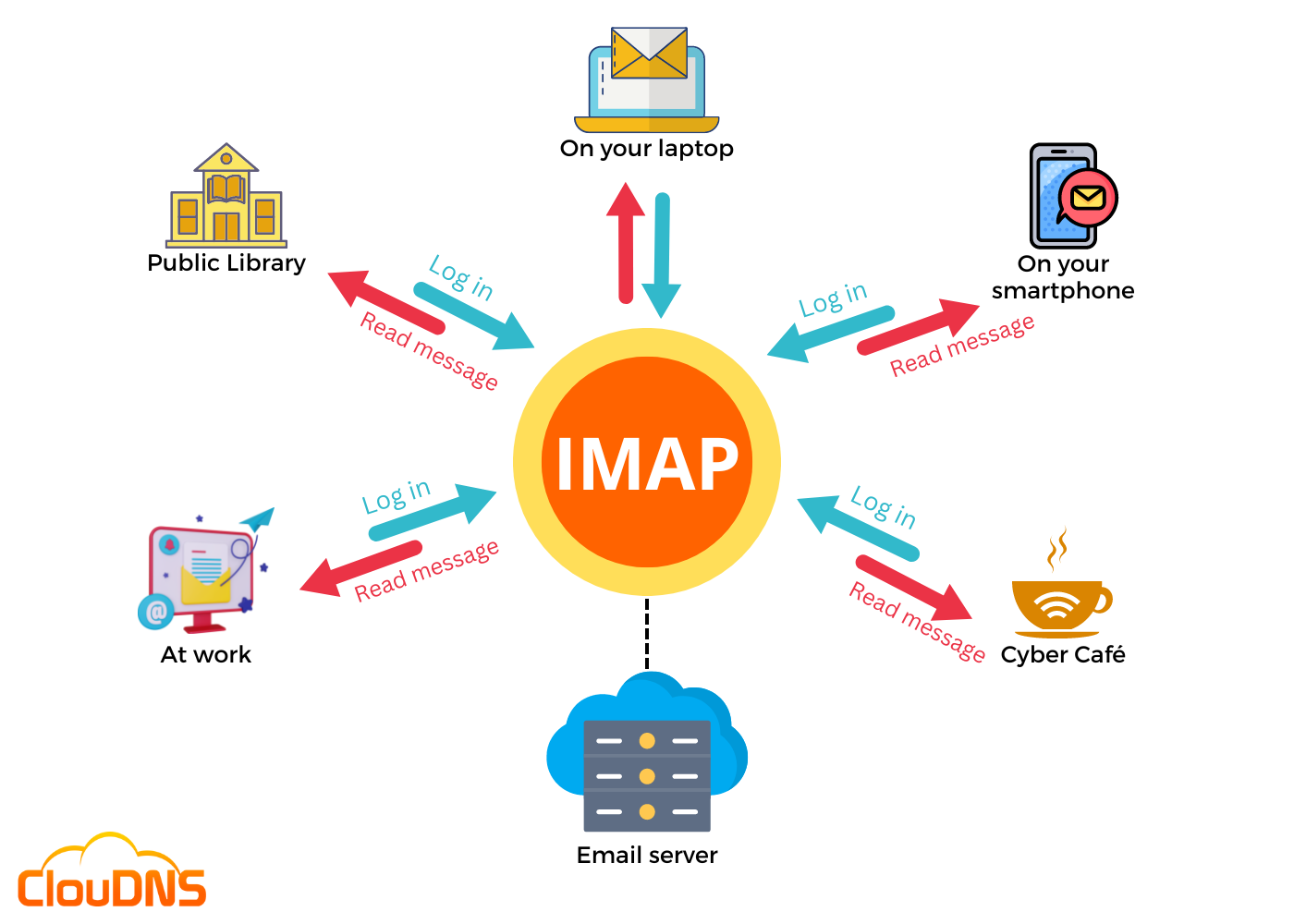
Internet Message Access Protocol, as an incoming email protocol, operates in the middle of the email server and the email client. Additionally, when a user is using IMAP and wants to read an email, it reads it off the server. That means it does not download or store the email on a local device, and users can gain access from any location in the world with different devices, like laptops, smartphones, and tablets.
Here are the main steps and processes involved in an IMAP function:
- The user signs into the email client, like Microsoft Outlook, and the client reaches the server using IMAP.
- A connection is established on a precise port.
- The email client shows the headers of all emails.
- Only when the user clicks on a message IMAP download it. Additionally, attachments do not download automatically.
- It is easier and quicker to check an email with IMAP rather than with other email retrieval protocols, like Post Office Protocol (POP).
- Emails are stored on the server if the user does not delete them.
IMAP port
Similar to other applications on a local device, the IMAP protocol requires a logical point of connection to the Internet. More precisely, such a connection is known as a port. Therefore, prior to setting a connection to the Internet, every application needs to be bound to its assigned port, represented by a number.
There are two different ports that IMAP typically uses. They are the following:
- Port 143: It is the default port, and it is a non-encrypted IMAP port. It is known as unsecured because it does not provide any encryption.
- Port 993: It is the encrypted IMAP port (secure). It works over TLS/SSL encryption, and it is used when the user wants to connect through IMAP securely.
It is important to note that port 143 should not be open and accessible to the outside world on any account. That is because it is not secure, and some criminals can take advantage of it and initiate different attacks. Therefore, it is highly recommended to use the more secure port (993).
Features
Internet Message Access Protocol’s key features are:
- Multiple mailboxes: With it, users can manage several mailboxes and transfer messages between them.
- Organize emails: Users are able to organize their messages and create different categories and folders.
- Synchronization: It allows users to sync the folders across all their devices.
- Retrieve mail from the remote server: IMAP allows users to access their mail remotely while keeping the emails on the server.
- Set flags: It lets users implement message flags to track read and unread messages easily. The status of every message is saved, and the user can see it on every device.
- Check information before downloading: Users are able to view emails, and the email header, including the sender, subject, and date, before deciding to download.
- Download just a part of a message: IMAP lets users download only a portion of the message.
- Search: This feature allows users to search the contents of emails
- Hierarchy: IMAP lets users implement an email hierarchy based on the importance of the message.
How to use an IMAP server?
Email services like Gmail, Outlook, and Yahoo are pretty popular, and in case you are using one of them, you are familiar that when you make some changes to your emails, they are synced on all of your devices. Yes, exactly like IMAP!
That means if you set up an email account in one of these well-known email apps, the app configures it automatically by default as an IMAP account. As a result, the modifications you make to your email account will automatically sync with the webmail server.
In some rare cases, an email client could have problems with configuring an IMAP account. In such situations, it is best to contact the email service’s support for help. Sometimes it could be necessary to set up the account manually.
Benefits of using IMAP
Using IMAP supplies the following benefits:
- Access from anywhere: It lets you access your emails from everywhere and from as many devices as you like. This makes it ideal for people who need to stay connected across multiple platforms, ensuring that your inbox stays consistent and updated on all devices.
- Selective message downloading: Only when you click on a message it downloads it. That way, you are not wasting time waiting to download all of your new messages from the server to read them. This improves your efficiency, especially if you receive a large volume of emails or have limited bandwidth.
- Control over attachments: It does not download attachments automatically. That way, you can check your emails more quickly. Moreover, it gives you more control, and you can decide which attachments to open and which not. This feature can help save bandwidth and time, especially when dealing with large files.
- Offline usability: It can be used offline, similarly to POP. Once you reconnect, any changes you made, like reading, deleting, or moving emails, are synced to the server, ensuring your inbox stays updated across devices.
IMAP, for sure, is going to remain the preferred protocol option, especially for many people that have a busy schedule.
Limitations of IMAP
While IMAP offers significant advantages, it also has its limitations:
- Storage Dependency: Since IMAP stores your emails on the server, the amount of available server storage is crucial. If your email provider has limited storage, you may quickly run out of space, forcing you to delete emails or upgrade to a paid plan.
- Offline Access Limitations: Although IMAP allows for syncing of emails, accessing them offline can be a challenge. Most clients only download email headers or partial content. To read full emails and attachments offline, you need to ensure they’re downloaded in advance manually.
- Server Load and Speed: Constant syncing between the server and your email client can cause a higher server load, especially with large mailboxes or multiple users. This can result in slower performance, particularly if the server isn’t optimized for handling a large number of requests.
- Complexity in Email Management: IMAP can sometimes lead to email management confusion. Actions like archiving, deleting, or organizing emails into folders on one device may not always sync as expected across others, depending on the email client or server configuration.
Uses of IMAP
Here are some of the main usages of the Internet Message Access Protocol:
Compatibility with Other Applications
IMAP has the potential to act as a bridge and eliminate the integration gap between email clients. The majority of users have more than a single email account in the present day. IMAP allows retrieving copies of all emails stored on any email server. That way, email platforms such as Outlook, for example, are able to integrate with more email providers on their platform. As a result, it provides better and more useful email usage.
Access Emails from Several Devices
Thanks to IMAP, you can make use of multiple smart devices and access emails from them. There are so many different options, for instance, laptops and desktops, tablets, and of course, smartphones. You can access email on all of these various machines. In addition, the email clients on these devices are automatically synchronized with the email server, creating seamless access. When an email is read, replied to, deleted, or accessed in any way on one device, the change automatically appears on all devices. Moreover, it lets users access messages without downloading them on each device.
Offline Access Support
Some of the latest versions of IMAP, for instance, IMAP4, include enabled email programs that allow access to messages online and offline. That is extremely beneficial in cases when there is no Internet connectivity or it is poor quality.
Security Considerations
While IMAP is useful and flexible, it’s crucial to consider security when using this protocol. Here are some key security considerations:
- Encryption: Always use secure connections when configuring your email client for IMAP. Most email providers offer encryption over SSL and TSL. That way, it ensures that your emails and login credentials are protected during transmission.
- Strong Passwords: Use complex, unique passwords for your email accounts. Make sure to enable two-factor authentication (2FA) if available to add an extra layer of security.
- Phishing Awareness: Be careful when clicking links or downloading attachments from unknown or suspicious sources. Phishing attacks often target email users to gain unauthorized access to their accounts.
- Regular Updates: It is crucial to update your email client and operating system regularly. By doing so, you ensure that your system receives the latest security patches and improvements, which are essential to safeguarding your personal information and keeping your device secure.
- Email Backup: Regularly backup your emails to prevent the loss of important information due to accidents or cyberattacks. Some email clients and providers offer automated backup options that can simplify the process.
SMTP vs IMAP vs POP
When we talk about IMAP, it’s essential to compare it to two other email protocols: SMTP (Simple Mail Transfer Protocol) and POP (Post Office Protocol).
- SMTP (Simple Mail Transfer Protocol): SMTP is responsible for sending outgoing emails. It is the protocol used when you click “Send” in your email client. Without a doubt, it plays a crucial role in the email ecosystem.
- IMAP (Internet Message Access Protocol): IMAP is designed to handle your inbox across multiple devices. It synchronizes your email across all your devices and keeps messages on the server. That is why it is a preferred choice for those accessing their email from various devices.
- POP (Post Office Protocol): POP is an older protocol that downloads emails from the server to your device and removes them from the server. It’s less suitable for modern email usage, where you typically access your emails from more than one device.
What Happens If You Disable IMAP?
Disabling IMAP means your email client (like Outlook, Apple Mail, or Thunderbird) can no longer access your emails through that protocol. IMAP is what allows these apps to connect to your email server, sync messages, and keep everything up to date across devices. Once it’s disabled, any app using IMAP will stop syncing, meaning you won’t see new messages, and changes made in the app (like deleting or moving emails) won’t reflect on the server.
However, your emails themselves are not deleted. They remain stored on the mail server. You can still access them through webmail (like logging into Gmail.com or Outlook.com via a browser), or through another protocol if configured (e.g., POP3).
Disabling IMAP is sometimes done for security reasons or account management, but if you’re using multiple devices to access your email, it’s best to keep it enabled. Also, keep in mind that if you disable IMAP and later re-enable it, you may need to reconfigure your email client from scratch. Depending on the app, some locally stored data may be lost.
Conclusion
Internet Message Access Protocol (IMAP) brought up a lot more flexibility to the way we receive our emails. It is definitely one of the most important protocols, which provides us with easy and quick access to our email messages!


