You cannot imagine the internet without DNS. There is almost no service that doesn’t depend on DNS technology. E-mails, VoIP, web services, all kind of CRM and ERP systems and much more. DNS is so important that we must take care of our network and make it as secure as possible.
Here we will show you some good practices to manage your DNS. Prevention is the best defense. Pay attention to these pieces of advice and take action.
Table of Contents
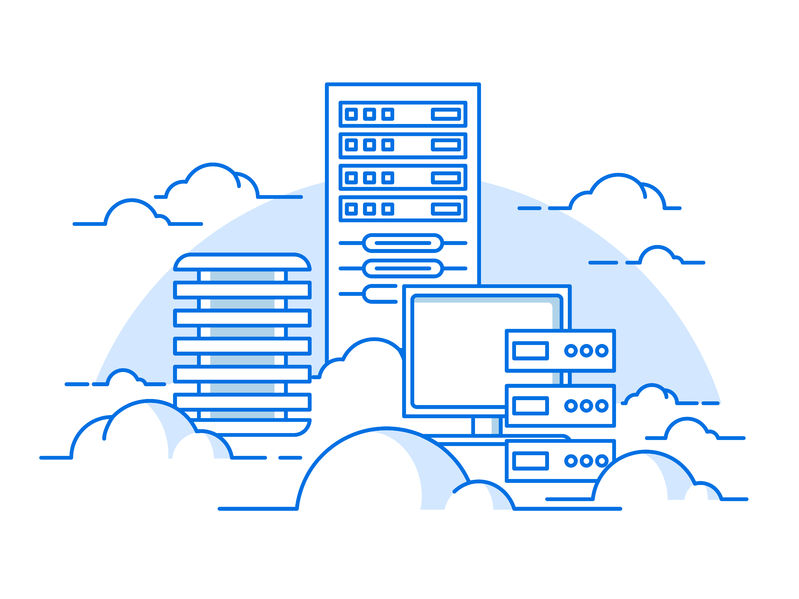
Hide the master DNS and Secure Access
Configure the master DNS as a hidden. Like this, it will not be shown in the records of the name server. It will not appear, and it will not respond to any queries. Its purpose will be to give zone transfers to secondary name servers which will be public but doing it safely and hidden. Also, restricting access to the master DNS ensures that attackers cannot manipulate or poison the records. Implement strict firewall rules to limit access to only trusted secondary servers, further strengthening security.
Furthermore, make the connection between the master DNS and the secondary name servers secured. Use ACLs (access control lists) and TSIGs (Transaction signatures). Like this, your secondary servers won’t be fooled, and your network won’t get corrupted.
Disable recursion and Add rate limits
Do this on the external servers and reduce the risk for your authoritative servers to be part of DNS attacks like DNS Amplification. Recursive DNS queries can be exploited for DDoS attacks. By disabling recursion, you prevent unauthorized users from leveraging your DNS servers for malicious activities. Always ensure that recursion is enabled only for trusted internal networks.
Even if you disabled the recursion on your authoritative DNS servers, they still could be used in DNS Amplification attacks with your domain names. To mitigate the options of the DNS attackers, you can add rate limits. If you are using bind software, here is an example configuration you can add to the options clause to set rate limit from 2 queries per second on average for each IPv4 class C (/24) network:
rate-limit {
responses-per-second 2;
ipv4-prefix-length 24;
slip 1;
};
Don’t show all information
The information about the version of your DNS software is for you. Don’t make it public. If hackers know it, they can use it against you by exploiting the particular vulnerabilities that the software might have. For example, if you are using bind software you can add a version in the options clause like this:
version “unknown”;
In addition, always make sure that sensitive information like OS version, patches, and other details related to the underlying infrastructure is hidden. Reducing the amount of exposed information is one of the simplest yet most effective ways to secure your system.
Place content (web) servers where your customers are
Be smart and think about your users. Place name servers where your clients need them the most. It will reduce the latency and improve the experience for your users. It will also minimize the load on your other servers, give you extra protection, and it will reduce the chance of failure. If you have multiple target markets in different locations (for example EU and the US), you can use GeoDNS service to direct the customers to the right servers which are closer to them.
By utilizing GeoDNS, it will optimize the distribution of user traffic based on geographic locations. By directing users to the nearest or least loaded server, GeoDNS reduces latency and enhances the user experience. This approach not only improves response times but also helps in managing traffic loads more efficiently across distributed networks. Additionally, GeoDNS can be configured for failover mechanisms, rerouting traffic seamlessly in case of server downtime, thereby increasing the reliability of services.
Ready for ultra-fast DNS service? Click to register and see the difference!Experience Industry-Leading DNS Speed with ClouDNS!
Anycast DNS
Use Anycast DNS for your business. This will make the experience for your users, faster and better. It will dramatically reduce the time to load the first page of your website, which helps your SEO significantly. It makes it more resilient, making it harder to experience a down time and more protected from DDoS attacks because of the different points of presence. In addition to improved redundancy, Anycast also helps distribute DNS queries across multiple locations, mitigating the impact of regional outages and improving failover response times.
Use DNSSEC
Domain Name System Security Extensions (DNSSEC) provide an additional layer of security on top of your DNS. This DNS best practice prevents a certain kind of attack where the attacker intercepts and potentially alters the DNS queries and responses. DNSSEC ensures that the users are communicating with the intended website or service, and not a malicious version of it. However, it’s important to note that DNSSEC can be complex to implement and manage and should be thoroughly tested before deployment.
Monitor & Control DNS traffic
Keep an eye on your DNS traffic. Unusual patterns or a sudden increase in DNS queries could signal a security breach or a DDoS attack. By leveraging monitoring services and implementing alert systems, organizations can quickly identify and mitigate any unusual DNS activity, minimizing the impact of potential threats.
Furthermore, an excellent defence against viruses, spyware, and other malicious traffic is to block it before it can infiltrate your network. That’s where DNS filtering comes in. This technique controls and restricts access to specific websites or content based on DNS queries. By implementing it, organizations can proactively prevent access to malicious or inappropriate websites, reducing the risk of malware infections, data breaches, and other cyber threats.
Keep log files
Maintaining logs of DNS server activity is another crucial DNS practices for security incident response and forensic analysis. These logs provide valuable information about DNS queries and responses, allowing organizations to identify and investigate security incidents. By analyzing the logs, organizations can understand the nature of the incident, track the source of the attack, and take appropriate measures to mitigate the impact. Additionally, DNS logs help meet compliance requirements, facilitate audits, and optimize network performance.
Log files also play an important role in identifying trends over time, helping organizations proactively detect anomalies that may indicate security vulnerabilities or inefficiencies. By regularly reviewing and archiving logs, businesses can ensure they have the necessary data for troubleshooting, performance analysis, and legal compliance in case of disputes or regulatory inquiries.
Regularly audit your DNS configuration
Regularly reviewing and auditing your DNS configuration can help you identify and fix any misconfigurations or security vulnerabilities. The audit should cover all aspects of the DNS setup, including checking for unnecessary open zones, ensuring correct IP address mapping, and validating DNS record settings. Using automated auditing tools can speed up the process, but manual checks are essential for catching issues such as unauthorized zone transfers or misconfigured records. Regular audits ensure that DNS configurations remain secure and reliable, minimizing the risk of a breach due to misconfigured settings or unpatched vulnerabilities.
Conclusion
These are some of the most recommended DNS practices. While there will be new threats, many of the DNS attacks happening these days can be evaded. No matter if your network is small or large, try to keep it safe and protected, by following our recommendations. Restrict access to some parts of the network, and remember that well-designed infrastructure is vital to your digital presence.




Unquestionably believe that that you stated. Your favourite justification appeared to be on the web the easiest factor to take note of. I say to you, I certainly get annoyed while folks think about concerns that they plainly don’t recognise about. You managed to hit the nail upon the highest and also outlined out the entire thing without having side-effects , people could take a signal. Will likely be back to get more. Thank you