SFTP Fundamentals: A Deep Dive into Secure File Transfer Protocol
In a world where data is constantly in motion – whether you’re sending files to cloud...
Understanding SYN flood attack
Imagine a tech gremlin relentlessly hammering at the door of a server, bombarding it with so many requests that it can’t keep up and...
How does OSI Application layer 7 DDoS attack work?
As cyber threats evolve, Distributed Denial of Service (DDoS) attacks have become more sophisticated and stealthy. Among the most complex...
What is SMTP Smuggling? How to detect and prevent it?
Email remains a critical communication tool, both personally and professionally. While it is...
Flood Attack: Prevention and Protection
In today’s digital age, security breaches and cyberattacks have become increasingly common. One such form of attack is the...
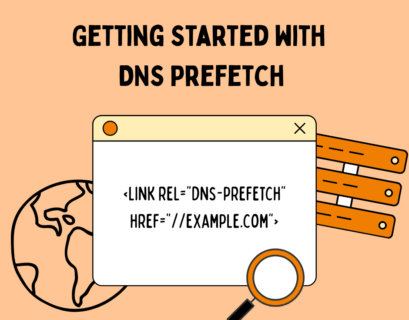
Getting Started with DNS Prefetch on Your Website
In the ever-competitive landscape of web performance, milliseconds matter. Whether you’re optimizing for Core Web Vitals, reducing...
R.U.D.Y. (R U Dead Yet) Attack Explained
In the ever-evolving landscape of cybersecurity, new threats constantly emerge, challenging the...
HTTP vs HTTPS: Why every website needs HTTPS today
In today’s digital age, securing information online has become more important than ever. One key aspect of online security revolves...
What are 301 and 302 Redirects and how to use them?
In the realm of website management and search engine optimization (SEO), proper redirection plays a crucial role in maintaining the...