DNS and SEO: How does DNS service affect SEO?
At first glance, you might think that there is nothing in common between DNS and SEO, but you will...
VPS (Virtual Private Server): An Introduction for Beginners
One of the most popular and versatile hosting solutions is a Virtual Private Server (VPS). Nowadays, businesses and individuals rely more...
Botnet – what is it, and how does a Botnet attack work?
Cybercriminals often use Botnet for their malicious purposes. That way, they build their army of devices and execute massive attacks. So...
What is DNS propagation? How to check DNS propagation?
In this article we’ll talk about DNS Propagation. But before that, we need to make sure you know...
What is a DNS zone? Primary and Secondary DNS zone and how to create it
A DNS zone is a fundamental part of how the Domain Name System organizes and manages data. It defines a specific portion of the DNS...
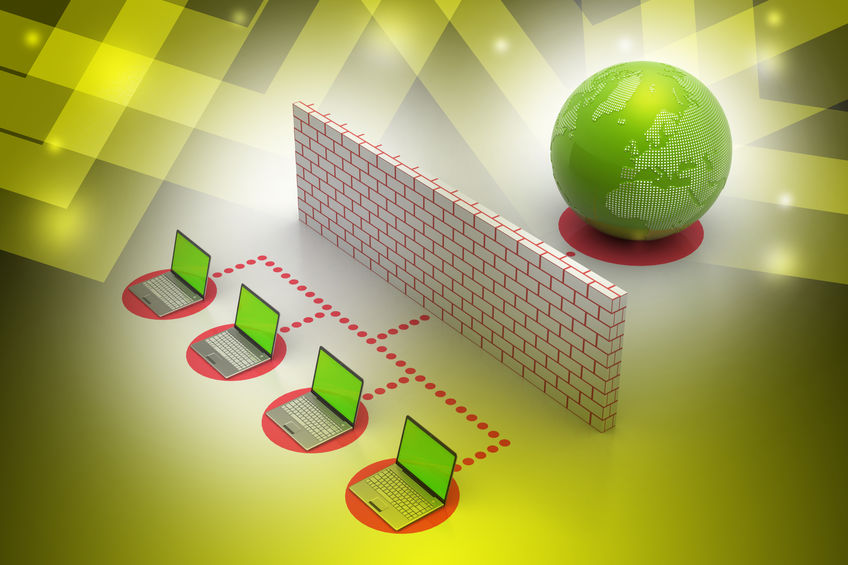
Router vs firewall, can you guess which is better?
Want to know the difference between router vs firewall? Great, you’re in the right place. In today’s interconnected world,...
DNSSEC, the DNS Security extension
The Domain Name System Security Extension (DNSSEC) is a powerful tool designed to protect both you...
What to Look for When Choosing a DNS Provider in 2025
Choosing the right DNS provider is critical in 2025. It impacts how fast your website loads, how well it handles traffic, and how secure...
Round-Trip Time (RTT): What It Is and Why It Matters
Round-Trip Time (RTT) is a fundamental metric in the context of network performance, measuring the time it takes for data packets to...
SMTP (Simple Mail Transfer Protocol) explained
SMTP (Simple Mail Transfer Protocol) allows us to send different emails to one another all the...