Why does DNS use UDP?
If you have ever wondered why DNS primarily relies on UDP (User Datagram Protocol) instead of other...
What is ICMP (Internet Control Message Protocol)?
The ICMP (Internet Control Message Protocol) is a network layer protocol and also a supporting protocol in the Internet protocol suite. It...
Getting Started with DNS Prefetch on Your Website
In the ever-competitive landscape of web performance, milliseconds matter. Whether you’re optimizing for Core Web Vitals, reducing...
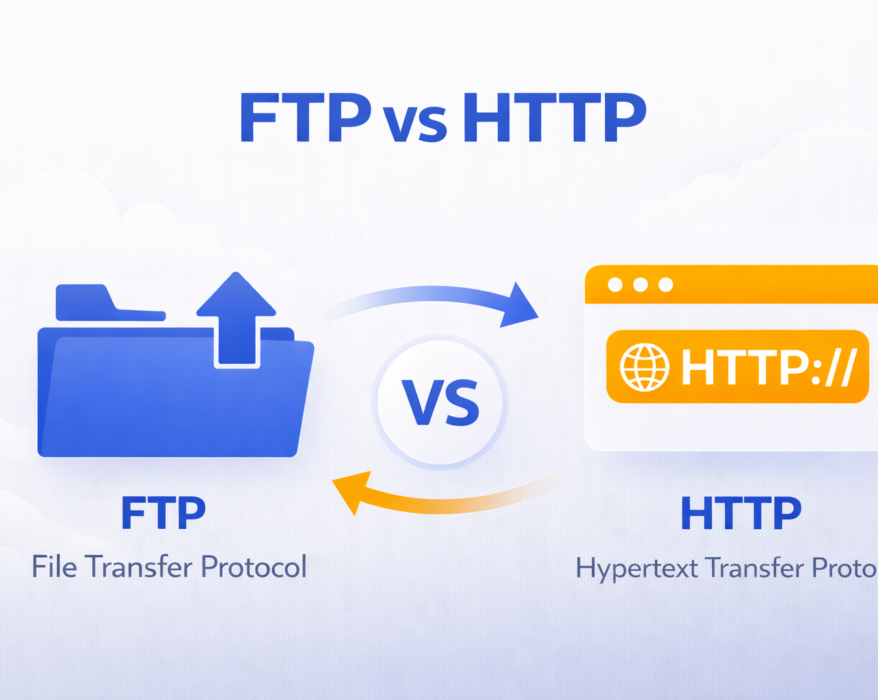
FTP vs HTTP: Understanding the Key Differences
Today we will see what exactly is FTP (File Transfer Protocol) and how does it compare to the newer...
Flood Attack: Prevention and Protection
In today’s digital age, security breaches and cyberattacks have become increasingly common. One such form of attack is the...
UDP (User Datagram Protocol) explained in details
UDP (User Datagram Protocol) is one of the well-known protocols in network communications. Thanks to it, we are able to watch video...
TCPdump for Beginners: What It Is, How to Install, and Key Commands
TCPdump is a powerful command-line tool for analyzing network traffic in real-time, making it...
QUIC Protocol Explained: What It Is and How It Works?
The internet is constantly evolving to deliver faster, more secure, and more reliable connections. From browsing websites to streaming...
Comprehensive Guide on TCP Monitoring vs. UDP Monitoring
Why does the battle between TCP monitoring vs UDP monitoring matter in the world of network management? In this guide, we’ll delve...
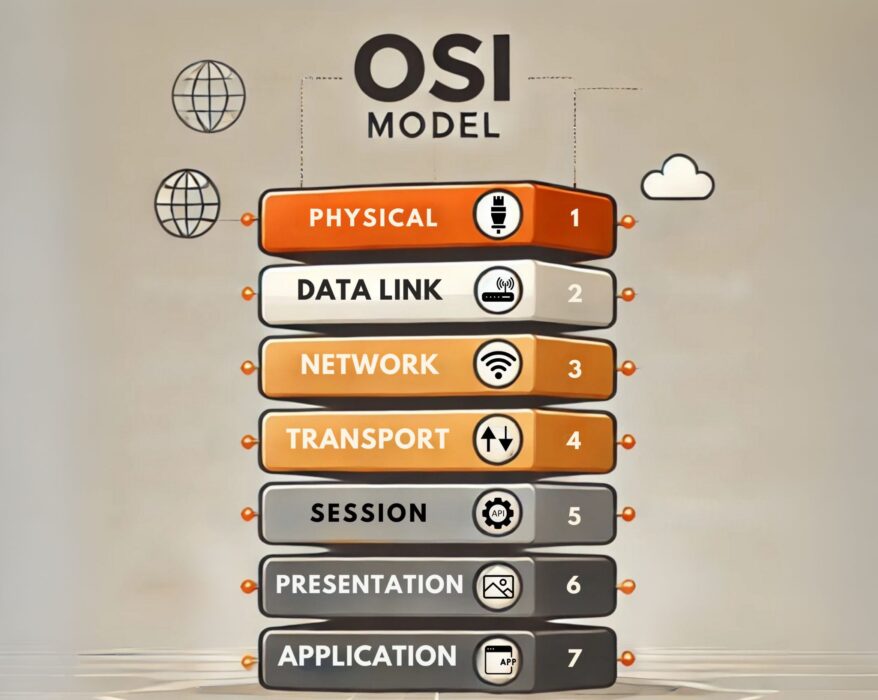
How do OSI Model layers work in computer networking?
In the vast realm of networking, the Open Systems Interconnection (OSI) Model stands as one of the...