Webhook Basics: Automate with Ease
Webhook is an amazing technology that facilitates seamless communication between different...
Understanding the HTTP status codes
Any now and then, when we are browsing the internet, we get one of those – error 500 or error 404. What does this number mean? How many...
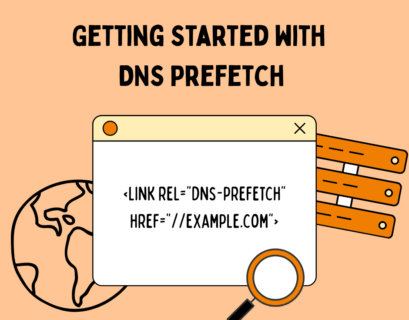
Getting Started with DNS Prefetch on Your Website
In the ever-competitive landscape of web performance, milliseconds matter. Whether you’re optimizing for Core Web Vitals, reducing...
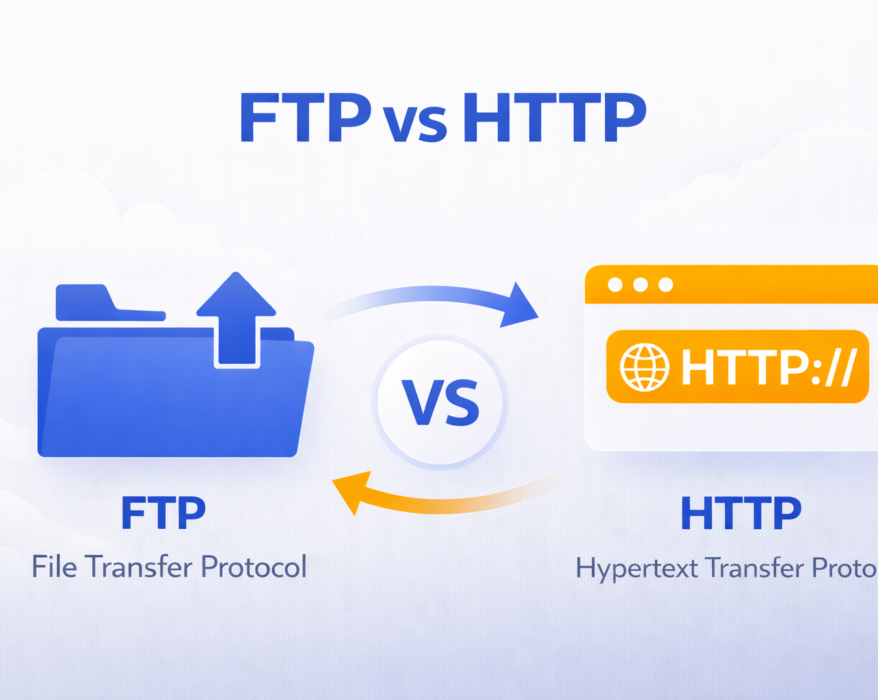
FTP vs HTTP: Understanding the Key Differences
Today we will see what exactly is FTP (File Transfer Protocol) and how does it compare to the newer...
How does OSI Application layer 7 DDoS attack work?
As cyber threats evolve, Distributed Denial of Service (DDoS) attacks have become more sophisticated and stealthy. Among the most complex...
HTTP vs HTTPS: Why every website needs HTTPS today
In today’s digital age, securing information online has become more important than ever. One key aspect of online security revolves...
Top 10 cURL Commands for Web Developers
As a web developer, one tool you’ll frequently turn to for interacting with servers, testing...
TCPdump for Beginners: What It Is, How to Install, and Key Commands
TCPdump is a powerful command-line tool for analyzing network traffic in real-time, making it indispensable for network administrators and...
QUIC Protocol Explained: What It Is and How It Works?
The internet is constantly evolving to deliver faster, more secure, and more reliable connections. From browsing websites to streaming...
Comprehensive Guide on TCP Monitoring vs. UDP Monitoring
Why does the battle between TCP monitoring vs UDP monitoring matter in the world of network...