WordPress vs Drupal, which CMS to choose?
WordPress vs Drupal, which one is better and in what? These are two of the most popular content...
MAC Address: Everything You Need to Know
A MAC address is a unique identifier assigned to every device that connects to a network. Whether you’re using a smartphone, laptop,...
UDP (User Datagram Protocol) explained in details
UDP (User Datagram Protocol) is one of the well-known protocols in network communications. Thanks to it, we are able to watch video...
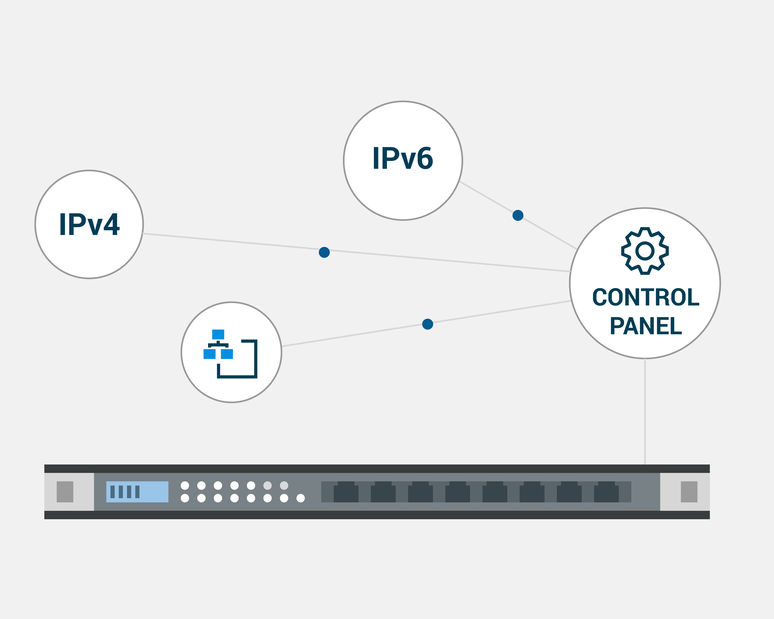
IPv4 vs IPv6 and where did IPv5 go?
Every time you see some network settings, there are IPv4 or IPv6 addresses. As you can guess, the...
What is IPv4? Everything you need to know
Nowadays, in this rapidly evolving global Internet world, we can’t skip the IPv4. It is the most used IP currently and still resists...
Drupal. Is it a good CMS?
Have you bought a domain and don’t know how to start your site? What platform should you choose? There are plenty of CMSs (content...
Basic DNS terms you should know (List + Infographic)
What is DNS (Domain Name System) The Domain Name System (DNS) is often compared to a phonebook, and...
IoT (Internet of Things): A Complete Overview
In the past two decades, no technical innovation has reshaped the way we live, work, and interact more than IoT (Internet of Things). From...
What is a Teardrop attack, and how to protect ourselves?
The Teardrop attack is a cyber threat that should not be neglected. It could affect you or your...