Whitelisting vs Blacklisting, preventing or reacting
There are different security methods out there, but when it comes to data filtering, there are two...
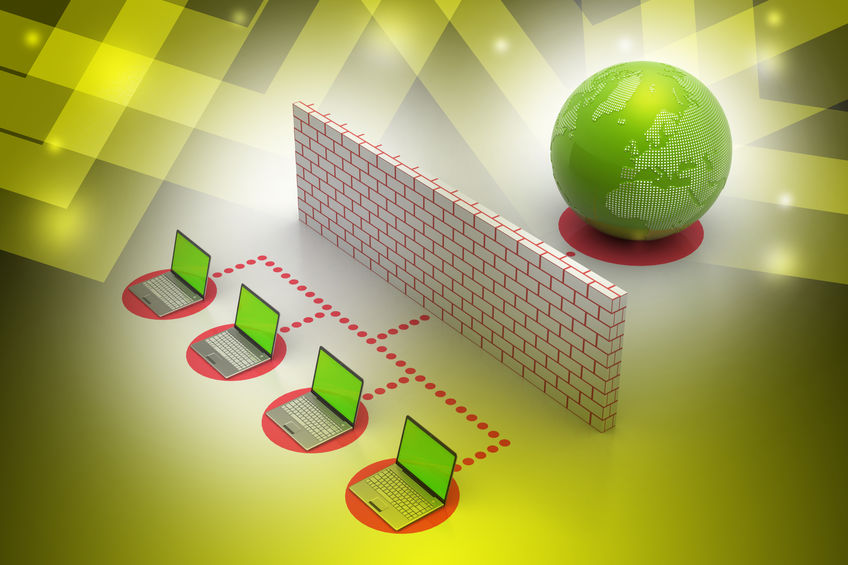
Router vs firewall, can you guess which is better?
Want to know the difference between router vs firewall? Great, you’re in the right place. In today’s interconnected world,...
DMARC, the solution for your phishing problems
DMARC emerges as the solution for phishing attacks that are a real danger for every business. They can severely damage the brand name, and...
DNS Failover, the backup that keeps your site online
It is Monday, you just entered the office, and it is a total mess. Apparently, during the weekend...