What is DNS filtering? Do you need it?
DNS filtering helps organizations keep networks and users safe by blocking access to malicious and...
Round Robin Load Balancing. Simple and efficient
In this article we will focus on Round Robin Load Balancing. Such techniques are important because the traffic on the internet is...
Hub vs. switch. What should you use for your network?
You want to create a network for the computers in the office, but you don’t know what to choose – a hub vs switch. Hub vs. switch, they...
What is a Certificate Signing Request (CSR) and How to Generate It?
Securing your website with SSL/TLS certificates is crucial for protecting sensitive data and...
DDI explained in detail
It is usually possible to hear the acronym DDI commonly mentioned when discussing network optimization. The funny thing is that it actually...
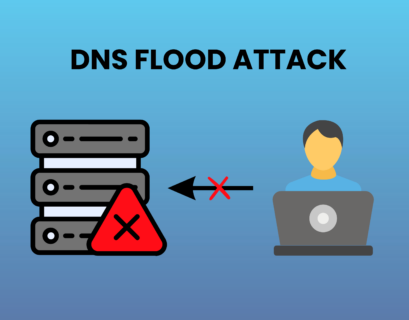
DNS flood attack explained in details
In the ever-evolving landscape of cyber threats, a DNS flood attack stands out as a formidable challenge for businesses and individuals...
What is TLD?
The TLD is one of the fundamental things you will have to consider when choosing a domain name once...
What is SSH?
You may have heard about SSH due to the fact it is often mentioned for anything associated with cyber security. It appears as a very...
What is Load Balancing?
Only an incredible technique like Load balancing can help you improve your performance, optimize your website, provide redundancy, and...
Error 404 Explained: The Page Not Found Mystery
Every internet user has encountered the terrifying “Error 404: Page Not Found ” at some...